The use of video conferencing platforms has grown as people need to isolate themselves due to the global coronavirus outbreak. Specialists in a hacking course mentioned that one of the companies that have won the most users in recent weeks is Zoom videoconferences. However, multiple members of the cybersecurity community have pointed to the serious security issues affecting this platform, forcing users to look for safer options.
One of these options is Jitsi, a project consisting of a set of free and open source tools to provide a video conferencing service secure enough for individual users and public and private organizations on multiple platforms. Its developers even claim that authoritative privacy voices, such as Edward Snowden, have endorsed this project.
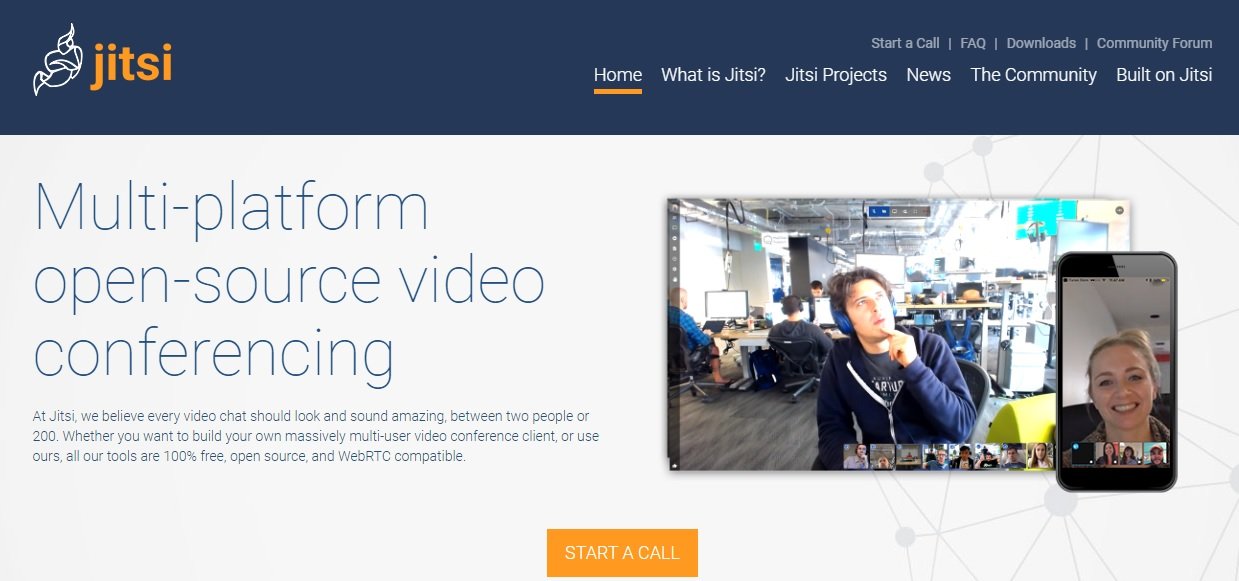
The main advantage of Jitsi is that, unlike its counterparts, it does not require the installation of a software or tool; in addition you do not need to create a user account, whether it is used on a desktop computer or on a mobile device, the specialists of the hacking course pointed out.
While Jitsi sessions do not have end-to-end encryption (as well as Zoom) and some data could end up in Google’s hands due to the default use of Google Analytics, as an open source tool developers can collaborate with the project and implement slight modifications to remove this feature and make Jitsi as private as developers want.
Another advantage is that there is no limit to the number of participants in a Jitsi session, so this variable is only subject to what is allowed by the bandwidth and capacity of the server. Users can modify the resolution of audio and video to establish greater control over the number of participants in the meeting. It should be noted that, in case of not using the default server, Jitsi has a function to host the session on the user’s computer.
In addition, the experts of the hacking course who have analyzed it consider that Jitsi is a very simple platform to use, because when entering the website there is only the option to create or join a videoconferencing room, not forgetting that Jitsi has some tools that will allow the organized intervention of all the participants of the meeting, such as chat via text messages or a function to virtually “raise the hand”.
The International Institute of Cyber Security (IICS) recommends visiting the official developers’ platform for more details on Jitsi and its functions.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











