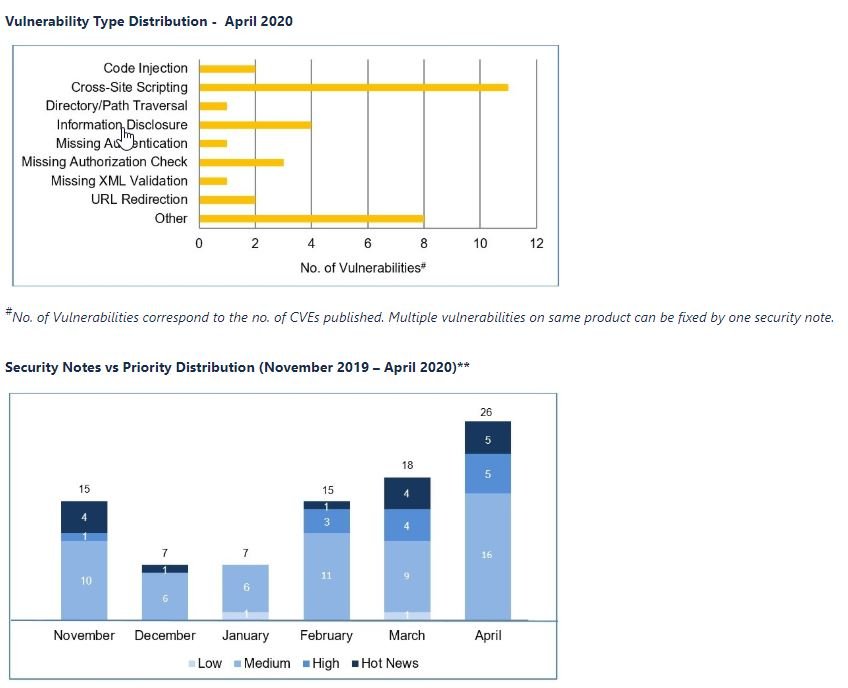
SAP developers have just released their latest security update package, which includes a total of 23 patches to fix various vulnerabilities, including five critical flaws in Hot News. According to the report of a hacking course team, the most severe of these flaws could lead to the compromise of SAP Commerce.
Tracked as CVE-2020-6238, the flaw received a score of 9.3/10 on the Common Vulnerability Scoring System (CVSS) scale, and could be exploited remotely and without authentication on the target system.
Hacking course specialists claimed that a threat actor could exploit the security flaw to access files and sensitive information on the network; in some cases, the malicious hacker could affect the functionality of the various SAP and Oracle services.
In addition to these reports, SAP announced the correction of a vulnerability in SAP NetWeaver Information Management, a centralized access point for users to search for directories, manage files, and other tasks. The flaw was tracked as CVE-2020-6225 and, if exploited, could allow a threat actor to load, overwrite, delete, or corrupt arbitrary files with arbitrary input validation.
The company also issued a security notice about a malicious code injection vulnerability. Tracked as CVE-2020-6230, this flaw includes authentication and script execution, and received a score of 9.1/10 on the CVSS scale, mentioning hacking course specialists.
Security patches also contain five high-priority security notes, the primary refers to the absence of an authentication control in the SAP Solution Manager. This vulnerability, tracked as CVE-2020-6235, can allow a threat actor to read sensitive information or abuse a component’s authentication control to access high-privilege administrative functions.
More priority bugs were fixed in the April update, including a bug present in Business Objects and Business Intelligence Platform. Tracked as CVE-2020-6237, this vulnerability consists of an escalation of privileges on the affected systems. The last of the reports relates to CVE-2020-6208, a vulnerability in Crystal Report that received a score of 8.1/10 on the CVSS scale.
All other flaws were present in ERP &S/4 HANA, NetWeaver, Fiori Launchpad, Company Client, S/4 HANA and SAP Commerce. These vulnerabilities are considered medium priority and no attacks have been presented in real-world scenarios.
For further reports on vulnerabilities, exploits, malware variants and computer security risks you can access the Website of the International Institute of Cyber Security (IICS), as well as the official platforms of technology companies.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











