Malware analysis is one of the most complex tasks in the cybersecurity community, mentioning security testing course specialists. One of the most reliable tools for malware analysts is the Linux-based set known as REMnux, which for more than ten years has supported cybercrime combating.
Because it brings together hundreds of different free tools for activities such as digital forensics, incident response, malware analysis, among others, REMnux has become one of the most effective initiatives in combating malware and preventing catastrophic infections that could compromise the operations of companies and government organizations.
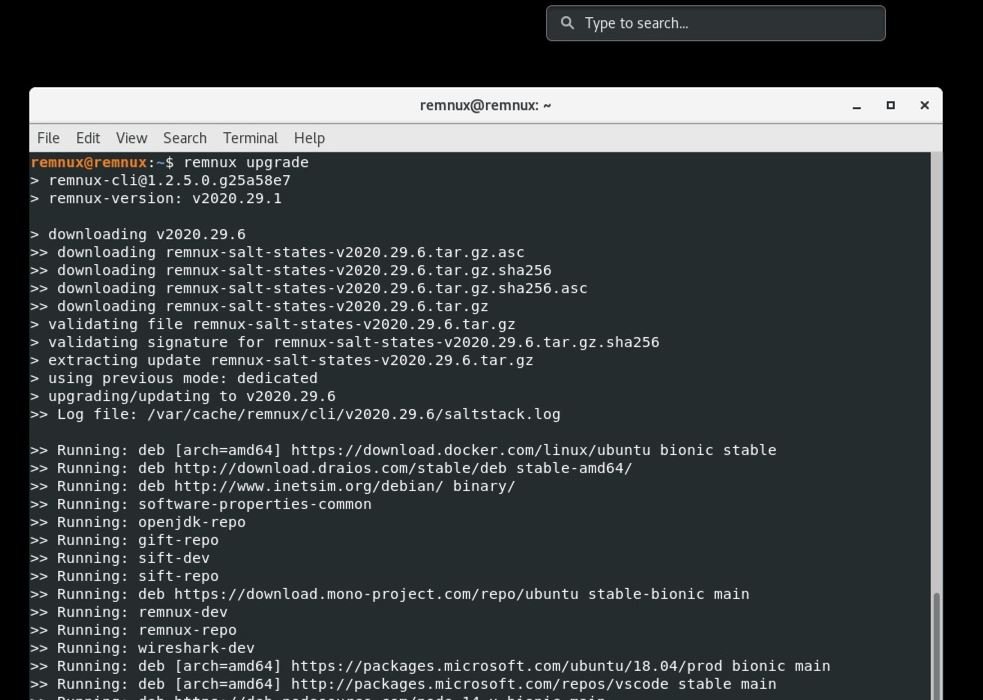
Another appeal of REMnux is its continuous reconstruction, mentioned by security testing course experts. Thanks to this, the developers keep the tool up to date, so the advancement in malware development is not a significant advantage for cybercriminals. For this, REMnux now has SaltStack that allows automation of the installation and configuration of the analytics software, as well as including a new architecture that facilitates feedback with the cybersecurity community.
Among the main features of REMnux we can find:
Windows Executable Scanning
- Static properties
- Chains and deofuscation
- Code emulation
- Decompilation
Linux binary reverse engineering
- Static properties
- Decompilation
- Debugging
- Behavioral analysis
Analysis of other forms of malicious code
- Android: apktool, droidlysis3.py, etc.
- Java: cfr, procyon, jad, jd-gui, etc.
- Python: pyinstxtractor.py, etc.
- JavaScript: js, js-file, objects.js, etc.
- Shellcode: shellcode2exe.bat, etc.
- PowerShell: pwsh, base64dump
- Flash: swfdump, flare, flasm, swf_mastah.py, etc.
Analysis of suspicious documents
- Microsoft Office files: vmonkey, pcodedmp, olevba, xlmdeobfuscator, oledump.py, etc.
- RTF files: rtfobj, rtfdump
- Emails: emldump, msgconvert
- PDF files: pdfid, pdfparser, pdfextract, pdfdecrypt, etc.
Regarding the decade of REMnux usage, the founder and main developer Lenny Zeltser, mentioned: “It’s hard to believe that it’s been 10 years since the release of the first version. During these years, this distribution became the most popular choice among malware analysts and reverse engineering experts.”
For security testing course experts, REMnux is as important for malware analysis as Kali is for pentesting. For further reports on vulnerabilities, exploits, malware variants and computer security risks, it is recommended to enter the website of the International Institute of Cyber Security (IICS), as well as the official platforms of technology companies.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











