Information security awareness specialists claim that a group of Chinese hackers recently tried to compromise the computer networks at the Vatican, operations allegedly sponsored by the Asian giant’s government.
These operations were detected by security firm Recorded Future, which mentions that the Chinese Communist Party decided to launch a campaign to increase its control over minority religious groups in China. Although the Chinese government officially recognizes five religions, including Catholicism, the authorities believe that religious cult interests could go against the Communist Party’s ideal, so they are sometimes treated as national security threats.
As information security awareness specialists report, Chinese government-sponsored hacker groups have undertaken multiple cyberattack campaigns with the intention of gathering as much information as possible about groups they consider subversive, such as Catholics, Buddhist Tibetans, Uighur Muslims, among other ethnic groups.
This time the hackers broke over the boundaries of Chinese territory, as the object of this attack is the Vatican and its Study Mission in Asia. This Hong Kong-based group serves as an intermediary in negotiations between the Catholic Church and the Chinese authorities.
The reason behind these attacks appears to be related to next September’s negotiations, when bishops will be appointed and decisions will be made on the state of Catholic temples in the Asian country. Cyberattacks would have started in May, information security awareness experts mention. It all started when an attack was detected using a legitimate-looking document sent to the Vatican that actually contained a malicious payload.
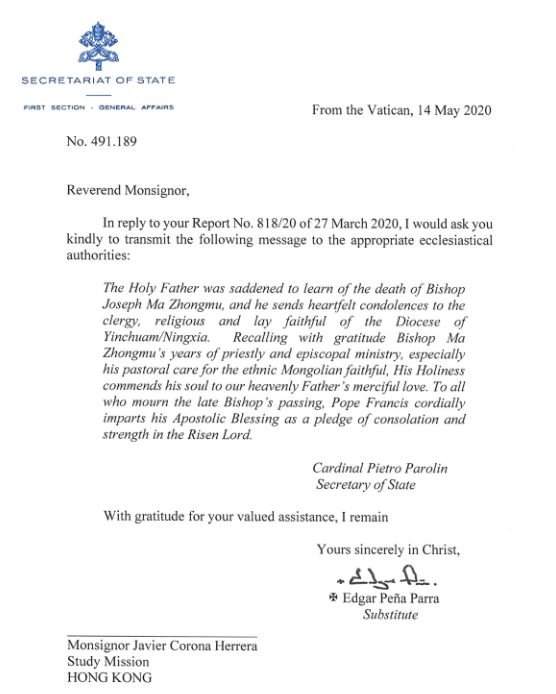
In fact, the email carried a message of condolences for the death of a bishop some time ago. It is not known whether this face was real or written by criminals, although it is a fact that was used as an access point to the compromised networks.
For further reports on vulnerabilities, exploits, malware variants and computer security risks, it is recommended to enter the website of the International Institute of Cyber Security (IICS), as well as the official platforms of technology companies.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











