Over a year after their last release, the new version of the network security scanner Nmap 7.90 has arrived, including multiple new features useful to security researchers.
The tool developers released the new version under their own Nmap Public Source License, aiming to get rid of the several restrictions established by the GPLv2 license.
This release was granted with more than 800 application and service version identifiers, and the total size of the identifier database has reached 11878 entries, as mentioned by the cybersecurity specialists. Besides, developers added nearly 400 operating system identifiers, 330 for IPv4 and 67 for IPv6. The program is able to identify 5678 versions of operating systems.
One of the main features included in this version is the addition of 3 new NSE scripts to provide automation of multiple actions with Nmap:
- dicom-brute for the selection of AET (Application Entity Title) identifiers on DICOM (Digital Imaging and Communications in Medicine) servers;
- dicom-ping to find DICOM servers and determine connectivity using AET IDs
- uptime-agent-info to collect system information from the Idera Uptime Infrastructure Monitor agents
The developers also created a special “Nmap OEM Edition” for companies licensing Nmap shipped with their products. The new installer is more tailored to the requirements of such products. A complete list of changes can be found in the developers’ official platforms.
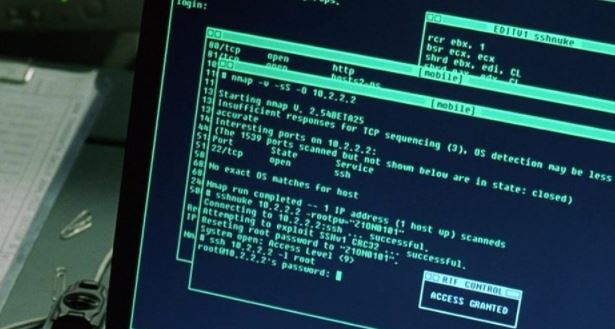
Nmap is a multi-platform network survey and security audit application. Supported scans based on a request for a response (determining the health of nodes), multiple methods of port scanning, versioning (which applications/services are running on the port) and analysis of TCP/IP traffic.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











