A group of threat actors allegedly sponsored by a nation state successfully attacked the systems of FireEye, a security company based in California, USA, as confirmed by the company itself through a detailed report. During the incident, malicious hackers stole some tools from Red Team, a team of research specialists using methods such as launching attacks in controlled environments.
Red Team specializes in mimicking the attack capabilities of the world’s most dangerous hacking groups, allowing the company to adopt better mechanisms to protect its customers. Over 15 years, Red Team has developed all kinds of scripts, tools and methods to improve the protection provided to its customers. Unfortunately, the company confirmed that many of these tools are now in the hands of cybercriminals.
According to the report, the compromised tools cover simple scripts for automating some projects up to complete frameworks similar to CobaltStrike or Metasploit. Many of the tools used by Red Team are now available to the cybersecurity community through CommandoVM, the company’s open source virtual machine. It should be noted that some of the available tools are used to evade basic security detection mechanisms.
The tools extracted by hackers did not contain zero-day exploits, limiting themselves to hacking methods widely known and documented by other security firms around the world. While the company rules out that these tools are very useful for hacking groups, it has been confirmed that the necessary measures will be taken to mitigate the potential risks arising from cyberattack.
So far no security incidents have been detected involving compromised tools, although FireEye will continue to monitor any potential criminal outbreaks.
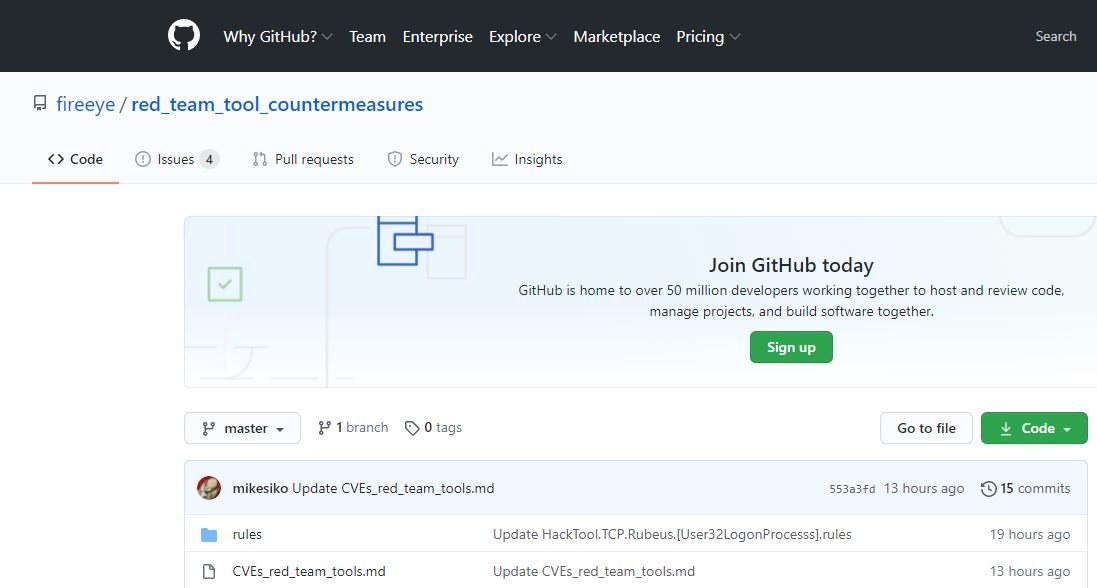
FireEye has issued a series of countermeasures to help its customers and the cybersecurity community identify whether any security incidents have occurred involving the tools exposed. Recommendations are available in the FireEye GitHub repository. The company also decided to launch detections and continue to update the public repository with overlapping countermeasures for host, network, and file-based indicators as we develop new or refine existing detections.
No additional details have been revealed about the hacking group responsible for the attack.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











