A group of specialists revealed the finding of a security flaw whose exploitation would have resulted in illegitimate access to more than 100,000 records of United Nations Environment Program (UNEP) staff. This data breach was due to a set of exposed Git directories and credentials, which gave unauthorized users access to the personally identifiable information of affected employees.
The report, prepared by Sakura Samurai, mentions that the committed resources are packed with documents and screenshots showing all kinds of personal details about the people affected.
This report was presented through the United Nations Vulnerability Disclosure Program by researchers Jackson Henry, Nick Sahler and Aubrey Cottle. Experts found the Git directories exhibited in domains associated with UNEP and the International Labor Organization (ILO), which also belongs to the UN. Researchers were able to clone the entire repositories of the .ilo.org and .unep.org domains using a tool known as git-dumper.
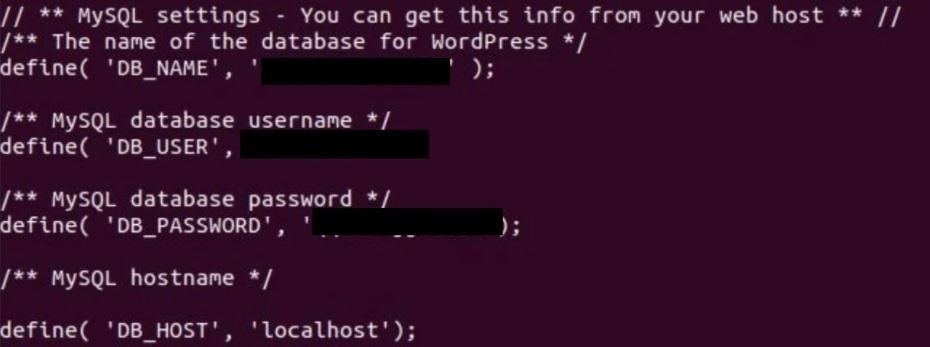
As shown in the following screenshot, the .git directory stores sensitive files, including WordPress configuration files, thus resulting in the exposition of the administrators’ database credentials.
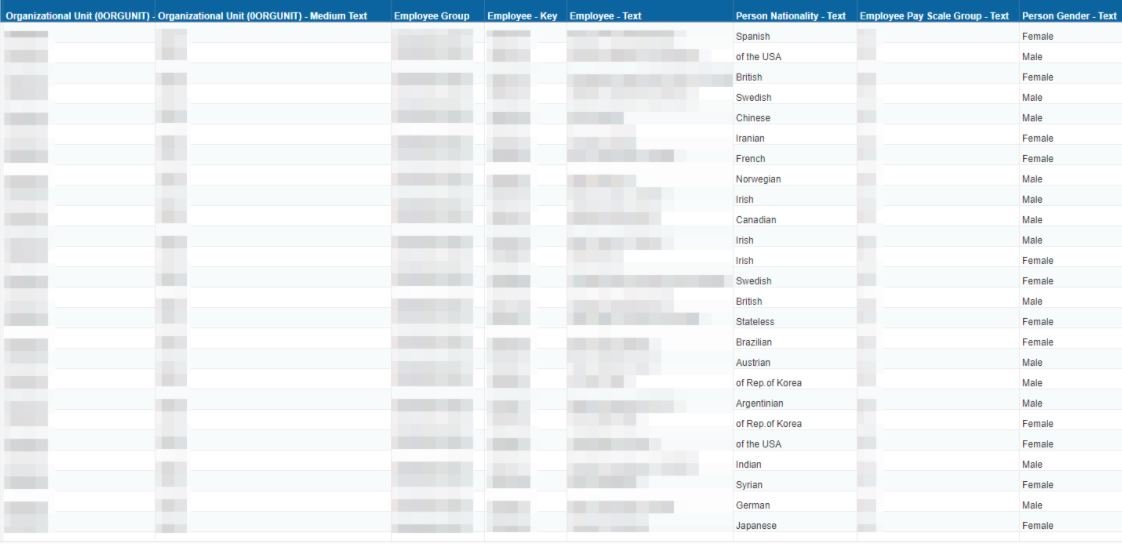
Using the compromised information, researchers were able to extract information from affected users, stored in multiple UN subsystems. In their sample, experts mention having found the travel history of hundreds of employees of the Organization, including full names, travel destination, dates, among other data.
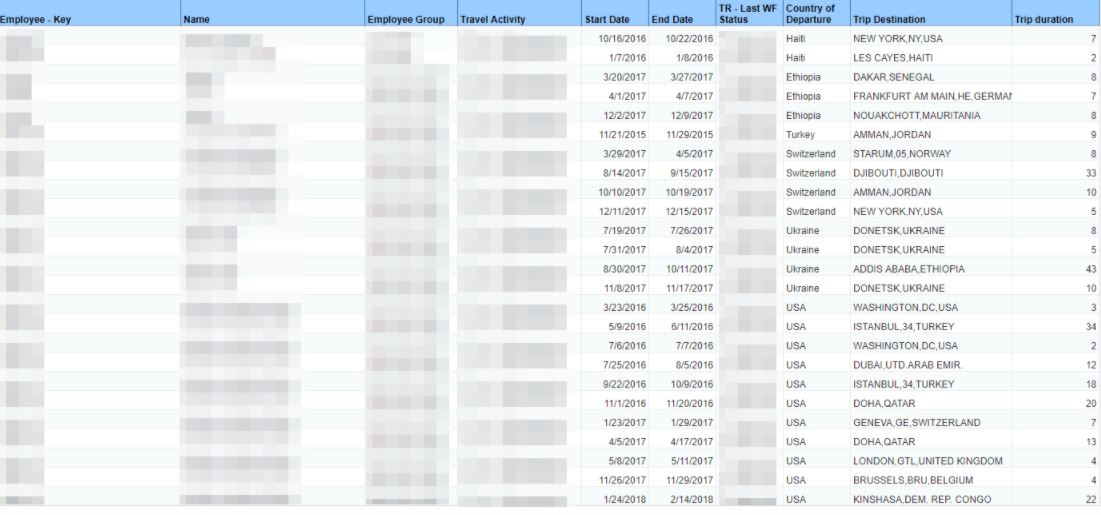
Other resources pledged included staff demographics, funding records, and employment assessment reports.
Although the United Nations recognized the report on the data gap, they mentioned to investigators that the failure caused by this leak is not related to the Work of the Organization: “The vulnerability reported does not belong to the United Nations Secretariat,” they report.
On the other hand, a representative of UNEP mentioned that the division was preparing for the disclosure of the incident, although it acknowledged that this was an unprecedented fact: “We would like to thank the specialists for submitting their report in application of the United Nations Disclosure Program; the incident will be corrected immediately.”

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











