SonicWall security team has issued a security alert related to a hacking group exploiting a zero-day flaw in its virtual private network (VPN) solutions that could allow the deployment of internal network attacks. SonicWall products are used by all kinds of small and medium and large businesses, so experts consider this to be a high-severity problem.
In its alert, released Friday, the company mentions that hackers have exploited this flaw in its Secure Movile Access (SMA) VPN device, as well as abusing the NetExtender VPN client in a sophisticated attack campaign: “We have identified a coordinated attack associated with zero-day vulnerability exploitation in some VPN products.” According to the report, the products affected by this malicious campaign are:
- NetExtender v10.x VPN client, released in 2020
- Secure Mobile Access (SMA) v10.x, used by SMA 200, SMA 210, SMA 400, SMA 410 and SMA 500v virtual appliance
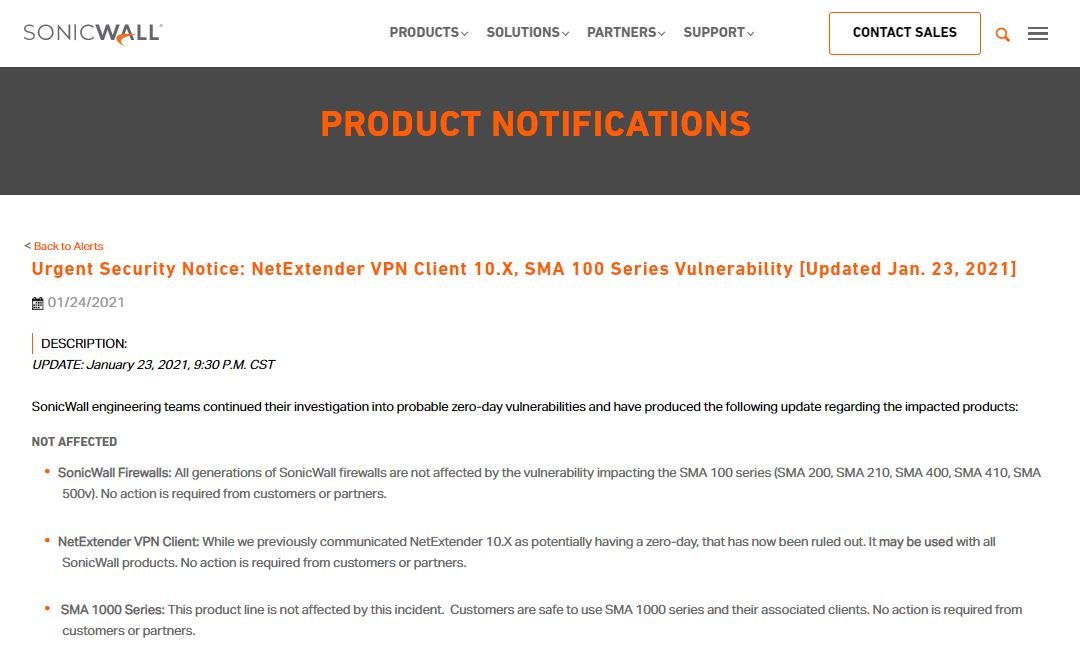
About the vulnerable products, SMA is a physical device that provides VPN access to internal networks, while NetExtender is a software client used to connect to firewalls that support the VPN connection. The report mentions that clients can mitigate exploit risks by enabling a multi-factor authentication mechanism on affected devices, as well as restricting access to a vulnerable device based on IP addresses considered legitimate by system administrators.
SonicWall published a report including detailed descriptions of vulnerable products, as well as a complete list of possible workarounds. At the moment the company will not reveal technical details about the flaws, although it is known that vulnerabilities can be exploited remotely on publicly accessible devices.
On the attacks detected so far, a cybersecurity report mentions that threat actors are fully aware of these flaws: “Various hacking groups claim to have information about a well-known firewall provider and other security solutions; big companies are especially vulnerable to these kinds of attacks,” the report states.
Exploiting flaws in VPN products is one of the main security threats for thousands of organizations around the world, as a successful attack would allow malicious hackers privileged access to compromised systems and even allow the deployment of subsequent attacks. Many of the most dangerous attack campaigns in recent times are targeting these kinds of solutions, so a greater approach to prevention is needed.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











