Netgear security teams announced the release of emergency firmware and security updates to fix 15 vulnerabilities in their JGS516PE Ethernet switch, including a remote code execution failure that can be exploited without authentication.
The vulnerabilities were reported to have been reported by NCC Group experts, who mention that most flaws affect the NSDP protocol, enabled for legacy reasons. The most serious flaw of all, tracked as CVE-2020-26919, received a score of 9.8/10 according to the Common Vulnerability Scoring System (CVSS) scale.
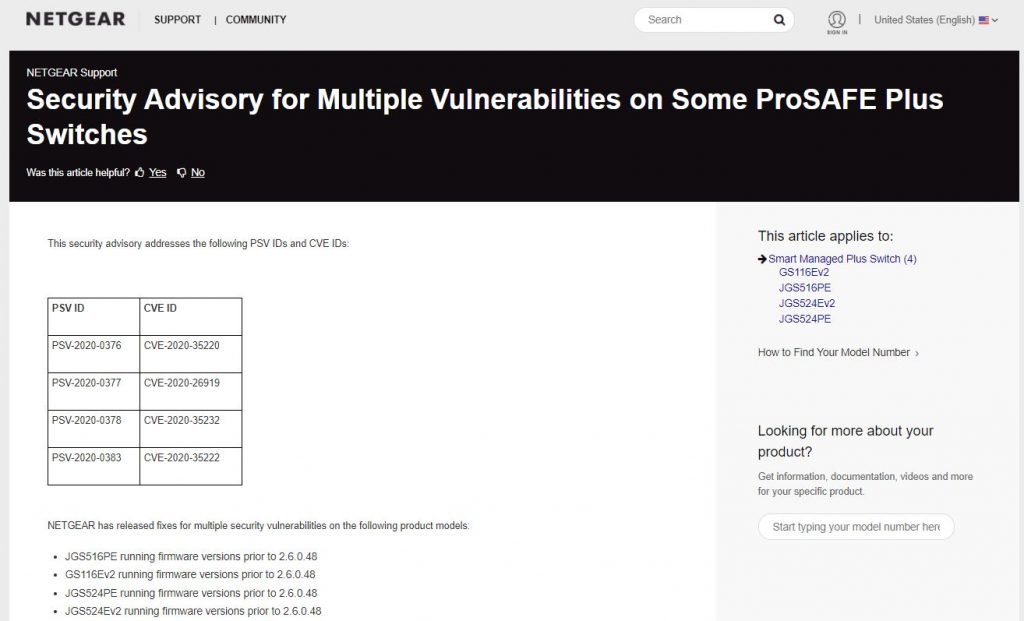
This flaw resides in the switch’s web management interface in firmware versions earlier than 2.6.0.43 and could be exploited by unauthenticated threat actors to bypass authentication mechanisms on the system and run tasks with administrator privileges.
“Each section of the web could be used as a valid endpoint to send POST requests being the action defined by the submitId argument. The problem is found on the login.html web page, which must be publicly available to make login requests, but does not implement any restrictions to execute debugging actions, allowing system commands to run,” the investigation notes.
“Affected versions cannot properly implement access controls on one of their endpoints, allowing unauthenticated hackers to bypass detection and execute actions with administrator privileges,” the report says.
Another failure fixed in this update is an NSDP authentication bypass tracked as CVE-2020-35231 that received a CVSS score of 8.8/10: “Vulnerable protocol is used by Netgear Switch Discovery Tool and ProSafe Plus Configuration Utility software”, experts add.
Finally, experts also found a flaw in the firmware update mechanism identified as CVE-2020-35220. A TFTP server with the ability to update firmware that is active by default could allow a threat actor to stealthily load malicious firmware updates: “This flaw even allows the installation of dangerous backdoors,” experts say.
Netgear released firmware updates for the JGS516PE switch on its website; the latest version available for download is 2.6.0.48, so users of vulnerable versions are invited to update as soon as possible to mitigate the risk of exploitation.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











