Security vulnerabilities are an issue that affects all kinds of technological devices and there is no way to ensure that any technological implementation is 100% invulnerable, whether it can be attacked by hardware, software or a combination of both.
One of the devices most exposed to exploiting vulnerabilities is the router; factors such as poor maintenance by companies and their massive use have made it one of the main objects of cyberattacks.
A research conducted by the Fraunhofer Institute for Communication (FKIE) analyzed 127 home-use routers from seven different manufacturers (Netgear, ASUS, AVM, D-Link, Linksys, TP-Link and Zyxel) that demonstrated the unusual number of vulnerabilities contained in these devices, even though some are operating on the latest updates.
In this research the experts focused on five different aspects:
- Release date of the latest firmware version of the router
- Operating system release date
- Techniques used to mitigate cyberattacks
- Using accessible private keys
- Type of default access credentials
According to experts, of the 127 routers scanned, 46 have not received security updates during the past year, exposing them to dozens (or even hundreds) of vulnerabilities. Updating routers also does not guarantee that they are safe; Researchers found that manufacturers often forget to include patches to fix the latest vulnerabilities, so they are still exposed to cyberattacks, not to mention that the estimated average time for a router to receive updates is 378 days.
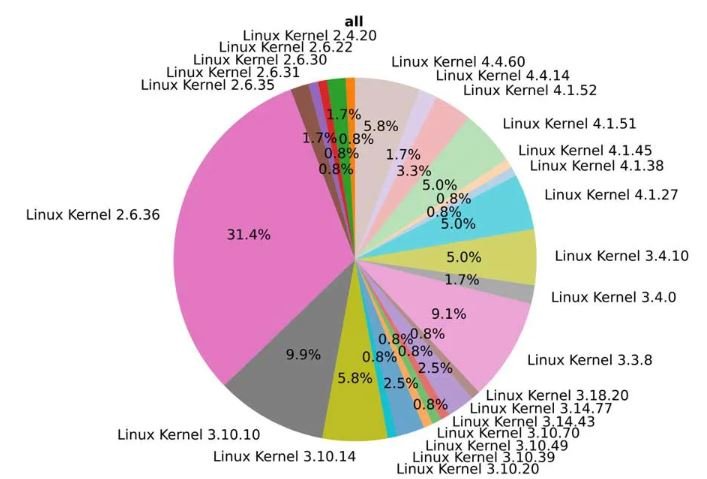
About 90% of the scanned routers work with Linux operating system, however, manufacturers do not update the system to implement changes made to the kernel by developers. Only 5.8% of routers use a Linux kernel later than version 4.4, the only one with extended support until 2022, cybersecurity experts mention.
Nearly two-thirds of routers use a kernel earlier than version 2.6.36, which stopped receiving support in January 2011, although one stands out among all. Experts note that the Linksys WRT54GL router uses the 2.4.20 kernel, released in 2002, making it the most vulnerable device for exploiting vulnerabilities (579 in total). The worst part is that this router is still on sale in multiple online stores, such as Amazon, although its use is very little recommended.
This is just a small effort to expose the magnitude of this problem from a small sample. Other similar analyses have yielded really similar results, so in the cybersecurity community this is undoubtedly a widespread problem.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











