A recent report notes that thousands of VMware vCenter servers exposed on the Internet are affected by a set of severe security flaws even after patches were released to address these issues. These flaws reside in vCenter Server, VMware’s centralized management interface.
The most severe flaws were identified as CVE-2021-21985 and CVE-2021-219896 and were corrected at the end of May.
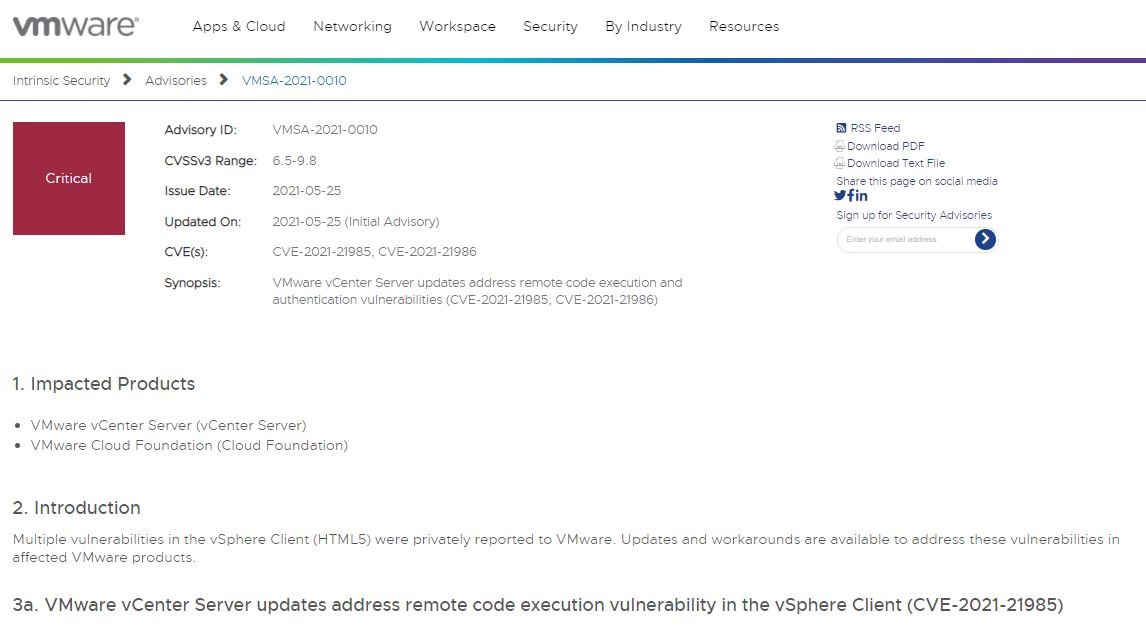
The first flaw lies in a vSAN plugin enabled by default and its exploitation would allow remote code to run in deployments with access to port 443. The flaw impacted VMware vCenter Server and VMware Cloud Foundation and received a score of 9.8/10 on the Common Vulnerability Scoring System (CVSS) scale.
In a security alert, the company mentions that the flaw can be exploited by a threat actor to access the adjacent operating system with high privileges.
On the other hand, CVE-2021-21986 resides in the vSphere Client and the vSphere authentication mechanism, including Virtual SAN Health Check, Site Recovery, vSphere Lifecycle Manager, and VMware Cloud Director Availability.
The flaw received a CVSS score of 6.5/10 and its exploitation would allow malicious hackers with access to port 443 to deploy actions allowed by the affected plugins without the need for authentication on the target system.
Early analyses indicate that there are thousands of servers connected to the Internet exposed to these flaws. This week, Trustwave researchers noted that a subsequent analysis revealed the detection of more than 5 thousand instances available online, most of them running port 443.
Using the IoT Shodan search engine, the researchers were able to find data from at least 4 thousand compromised instances, demonstrating that security patches have not been adopted by all affected version managers. Researchers estimate that nearly 20% of deployments available on the Internet are still exposed to flaws.
During the release of the updates, the provider company pointed out that the vulnerabilities require the immediate attention of users, so they must be updated as soon as possible. More information about the flaws and the update can be found on the company’s official platforms.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











