Microsoft Azure users running Linux virtual machines could be exposed to a severe security risk. According to a recent report, these implementations can be exploited remotely using a new, dangerous and stupidly easy method.
The report, published by Wiz.io, notes the detection of four vulnerabilities in Microsoft Open Management Infrastructure (OMI), which would allow threat actors to gain root access to a remote machine by simply sending a packet with a deleted authentication header.
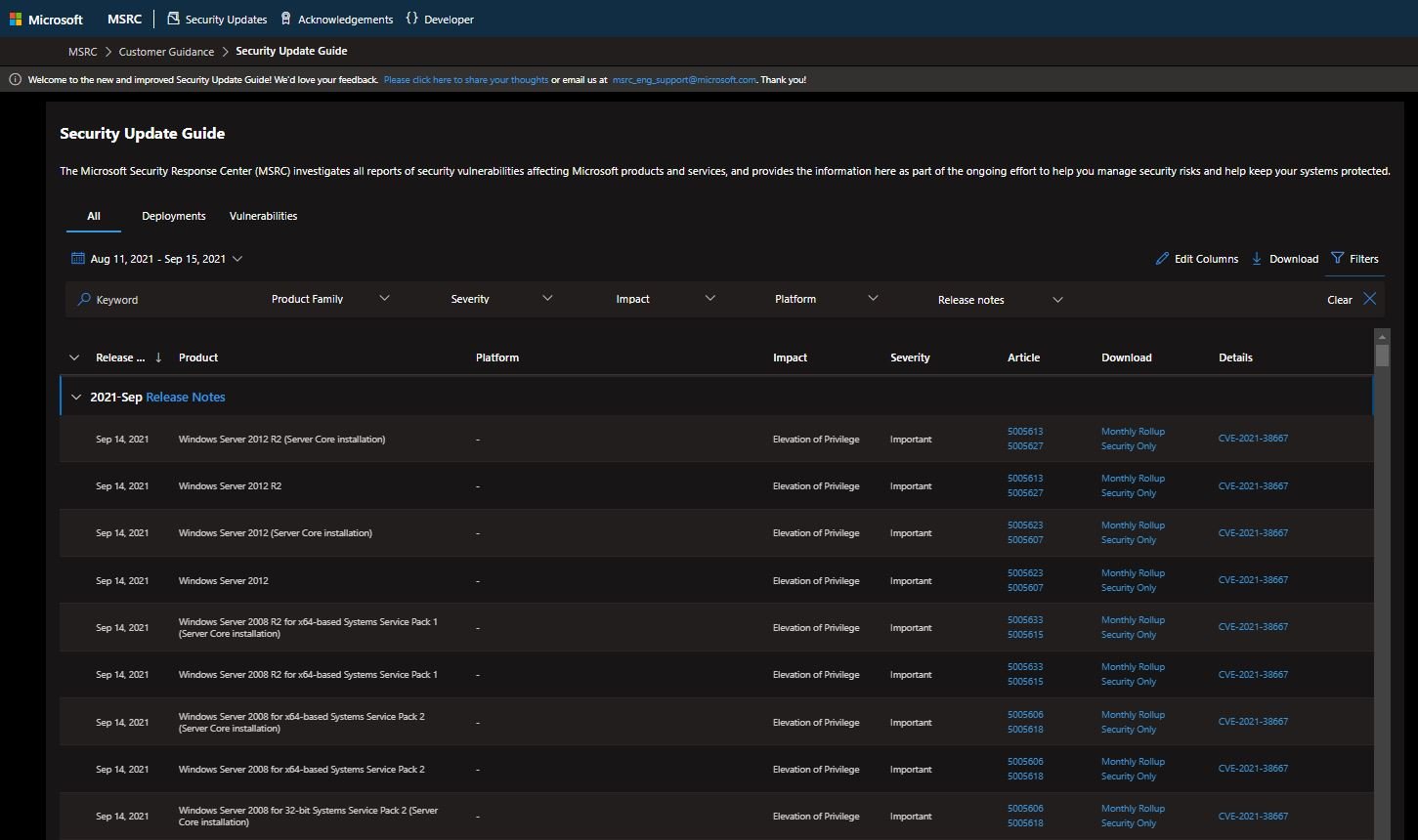
The vulnerabilities were tracked as CVE-2021-38647, CVE-2021-38648, CVE-2021-386485 and CVE-2021-38649. The flaws received scores between 7.0/10 and 9.8/10 according to the Common Vulnerability Scoring System (CVSS).
Nir Ohfeld, a security researcher at Wiz, described this flaw as “a textbook bug, very common in the ’90s but should be tremendously unusual in 2021 due to its ability to expose endpoints to trivial attacks with undesirable outcomes.”
The expert also mentions that, due to the combination of a simple encoding error and a non-initialized authentication structure, any request without an authorization header has default privileges such as uid=0, gid=0, which is equivalent to root user privileges. If OMI externally exposes ports 5986, 5985, or 1270, the system is affected by this vulnerability.
This appears to be a default setting when installed separately and in Azure Configuration Management or System Center Operations Manager. The good news is that other services like Log Analytics don’t expose these ports, so the risk is limited to local privilege escalations.
However, the risk to users is that OMI is installed stealthily along with log collection, plus it lacks public documentation and runs with root privileges. Wiz’s analysis concluded that approximately 65% of Azure customers running Linux virtual machines are vulnerable.
For security, users are advised to verify that their system is running OMI v1.6.8.1, in addition to turning to the company’s official platforms for further security recommendations.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











