This week Facebook unveiled its open-source static analysis tool used by its cybersecurity teams to detect potential security flaws in Android and Java apps. Dubbed as Mariana Trench, this tool is capable of analyzing millions of lines of code in a short time and thus prevents failures from reaching end users.
The social media giant says its security teams have found most of the bugs fixed in the company’s apps using Mariana Trench and other similar tools.
According to the report, the tool works by analyzing the flow of information from “sources,” which are sensitive user data such as passwords or locations to “sinks” (functions or methods that use data that originates from sources). Mariana Trench automatically detects these problems that could lead to severe security issues.
The company comments that, by default, Mariana Trench analyzes dalvik bytecode and can work with or without access to the source code: “A flow from sources to sinks can indicate that users’ passwords can be recorded in a file, something not recommended and that Mariana Trench will detect as a security error.”
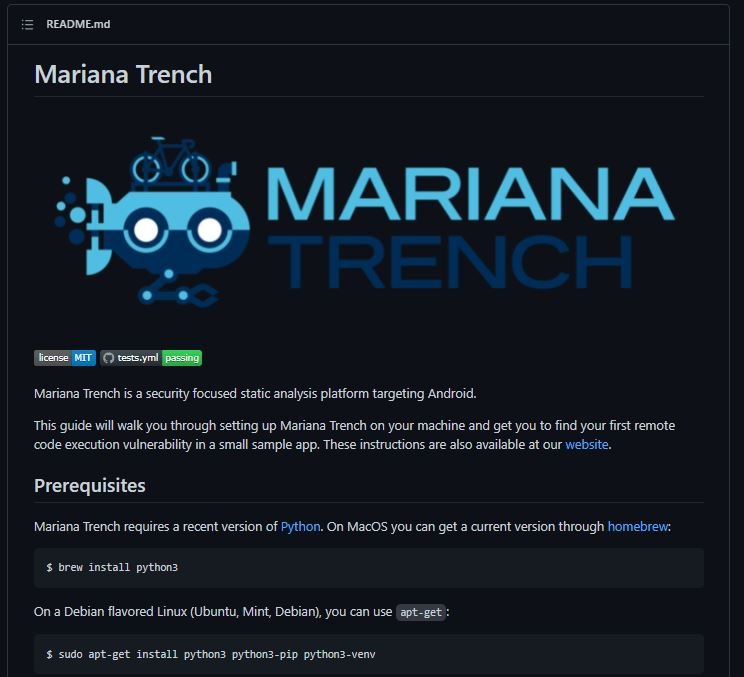
In addition, researchers can use the tool to focus on specific security issues, making some adjustments and adding new rules for automatic analysis.
Mariana Trench is not the only tool of its kind created by Facebook, since Pysa and Zoncolan were previously launched, for the analysis of Python and Hack code. These developments are available on GitHub and on its own website: “These tools were created specifically to detect flaws in Android applications. There are differences in patching and ensuring the adoption of code updates between mobile and web applications, so they require different approaches,” the Facebook report said.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











