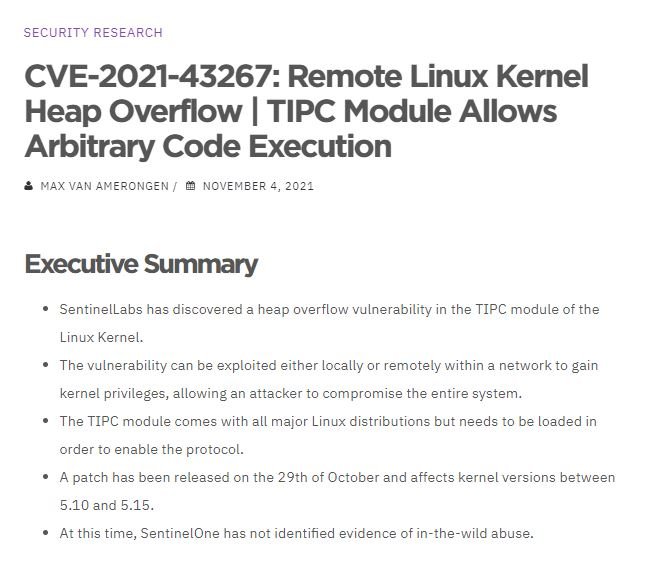
Cybersecurity specialists report the patching of a critical vulnerability in the Transparent Inter Process Communication (TIPC) module, implemented in the Linux kernel to facilitate communication within the cluster through Ethernet or UDP connections. According to the report, successful exploitation of the flaw would allow threat actors to execute arbitrary code on the affected module.
In the report, the vulnerability was described as a stack overflow bug that could be exploited locally or remotely in order to gain kernel privileges, which could completely compromise the affected system.
These findings have been made possible by the use of CodeQL, a semantic code analysis engine that allows users to perform code queries as if it were data, which made it easier to detect the error in the TIPC module.
SentinelOne experts found that a new user message identified as MSG_CRYPTO implemented as a new feature in this module in late 2020 was the cause of the problem. Although TIPC correctly validates the size of the messages, there is a validation failure for the keylen member of this message and for the size of the key algorithm names.
Threat actors could create specially crafted packages to allocate stack memory and then use an arbitrary size in the keylen attribute to perform out-of-bounds writing. Although local exploitation of the attack is less complex, remote exploitation is feasible due to the structures supported by TIPC. This flaw is present in kernel version 5.10.
At the moment reports of active exploitation are unknown, although it should be remembered that, although TIPC is included with the main Linux distributions, it must load to enable the protocol, so only implementations with this active function are exposed to an attack.
Researchers reported the flaw to Linux kernel maintainers in mid-October, who issued a security patch a couple of days later. Users of affected deployments are encouraged to upgrade to version 5.15, which contains the fix of this flaw.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











