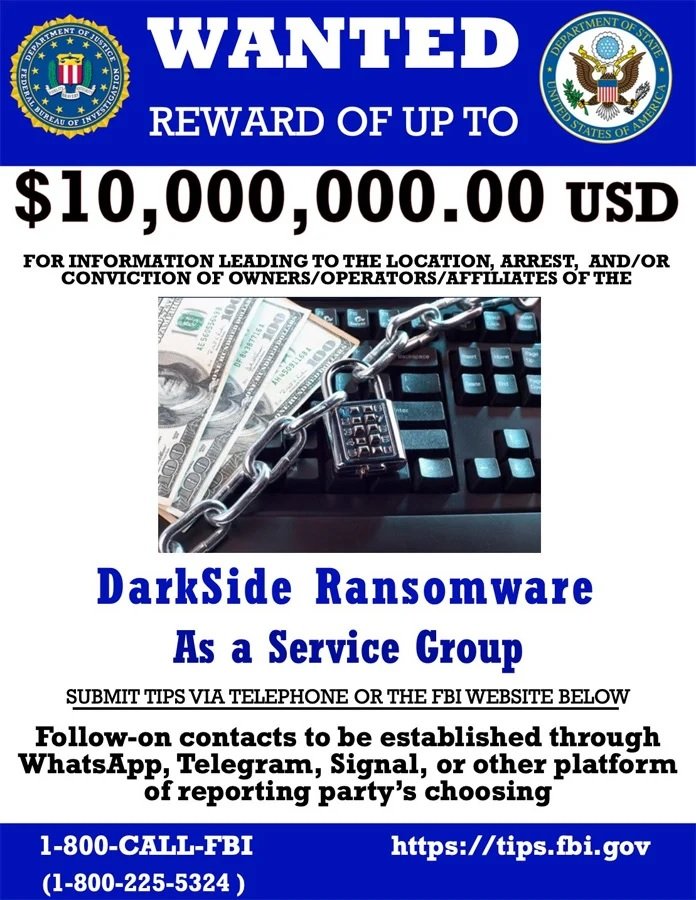
The U.S. Department of State announced that it is offering a reward of up to $10 million USD to anyone who provides information that leads to the identification and arrest of the operators of the DarkSide ransomware and any possible variants derived from this malware. Authorities are also offering a $5 million USD reward for information about those affiliated with this cybercriminal operation.
Those interested in participating in this special program can contact the authorities through the official website of the Federal Bureau of Investigation (FBI) and through messaging platforms such as WhatsApp, Telegram and Signal.
Authorities specify that the reward applies to variants derived from DarkSide, including name changes such as BlackMatter ransomware. It should be remembered that rebranding is a common practice among ransomware operators; when these groups feel cornered by the authorities, they decide to shut down their operation only to return a couple of months later, using another name but with the same malware variant.
In the case of DarkSide, this variant was rebranded as BlackMatter after the attack on Colonial Pipeline, which wreaked severe havoc and brought all U.S. authorities to the capabilities of ransomware groups.
This week, cybersecurity specialists reported that BlackMatter was about to close its operation, announcing the closure through its dark web platform. This does not appear to be an impediment for authorities to continue investigating members of this operation, whose identification and arrest has become a priority for the U.S. government.
Finally, the State Department announced a $10 million reward to anyone who provides information related to any threat actor sponsored by a national state, hoping to mitigate the hackers’ ability to mount a new cybercriminal infrastructure immediately after shutting down the previous one.
For further reports on vulnerabilities, exploits, malware variants, cybersecurity risks and information security courses fell free to visit the International Institute of Cyber Security (IICS) websites, as well as the official platforms of technology companies.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











