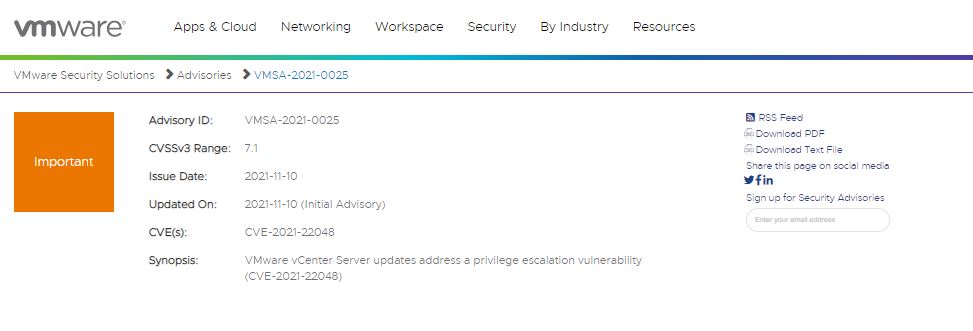
VMware developers released the detection of a privilege escalation vulnerability in vCenter Server. Tracked as CVE-2021-22048, the flaw received a score of 7.1/10 according to the Common Vulnerability Scoring System (CVSS).
According to the company’s report, threat actors with non-administrative access to vCenter Server could exploit the vulnerability to escalate their privileges to a group with greater access to critical areas in the system.
This flaw resides in vCenter Server v6.7 and v7.0, in addition to affecting Cloud Foundation 3.x and 4.x; the company recommends that administrators of affected implementations stick to the recommendations issued while the official update is released. Among the recommendations listed to mitigate the risk of exploitation is the change to AD over LDAPS authentication, from Integrated Authentication with Windows; at the moment the presence of other functional alternative solutions is unknown.
It is still unknown if the vulnerability has been exploited in real scenarios, although due to the absence of a security patch it becomes very possible to detect some cases of exploitation. The report of this vulnerability was attributed to researchers Yaron Zinar and Sagi Sheinfeld.
The Cybersecurity and Infrastructure Security Agency (CISA) also posted an alert, asking users to stay on top of any updates issued by VMware.
Finally, it is necessary to remember that there are multiple hacking groups dedicated to exploiting vulnerabilities in vCenter Server, so it is important for administrators of these deployments to stay on top of any new security risks related to these vulnerabilities.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











