A hacking group is abusing two legitimate Apple features to bypass the App Store security requirements and trick iPhone users into installing malicious apps hiding dangerous malware variants.
For years, Apple has required apps to pass a security patch to be supported in the App Store before they can be installed on end-user devices. This process prevents malicious apps from reaching devices and can trigger risk scenarios.
Sophos researchers detailed the detection of two methods employed in this campaign, identified as CryptoRom and based in cryptocurrency fraud targeting iOS and Android users. Unlike the Android system, iOS does not allow the installation of applications from third-party platforms.
The campaign depends on the abuse of TestFlight, an Apple service for beta testing of new apps. By installing TestFlight from the App Store, any iOS user can download and test apps that have not yet completed Apple’s strict verification processes, which threat actors tried to use to their advantage to compromise the devices of unsuspecting users.
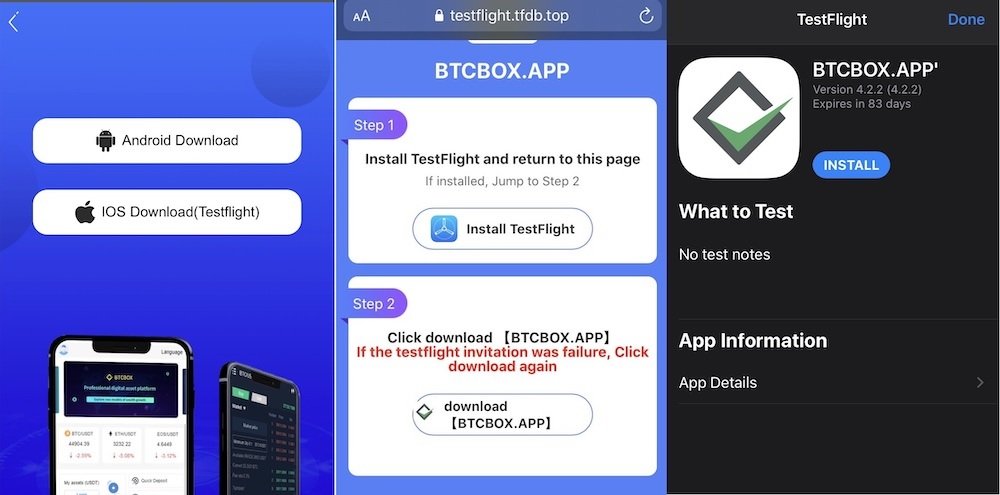
Sophos mentions that hackers contacted TestFlight users to convince them to install what appeared to be a new version of BTCBOX, a cryptocurrency exchange app. These users received a link that redirected to the fraudulent APK.
For the researchers, this attack vector allows for better evasion of App Store security measures, such as the Super Signature feature. This feature allows you to use an Apple developer account for limited delivery of some apps. The attack also abuses Developer Enterprise, a program for large enterprises to deploy applications for internal use.
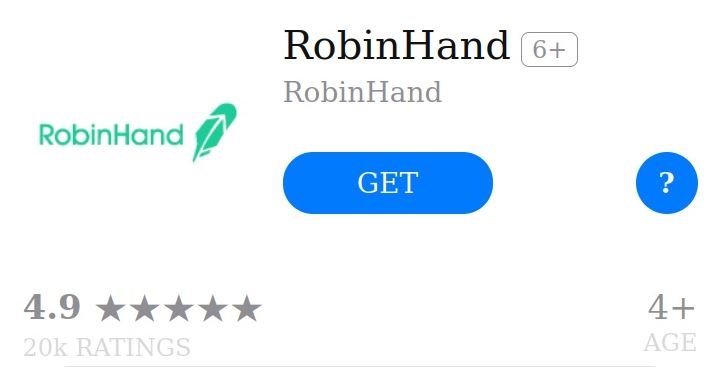
CryptoRom operators also exploit the Web Clips feature, which allows you to add a link directly to an iPhone’s home screen in the form of an icon that can be mistaken for a benign app; this item appears after a user has saved or copied a link. Sophos mentions that threat actors abuse Web Clips to add legitimacy to malicious URLs that redirect to fraudulent app downloads.
In the example below, hackers use a malicious app called RobinHand, intentionally designed similarly to the Robinhood investment platform.
This campaign relies heavily on social engineering, with threat actors resorting to all sorts of tricks to build a trusting relationship with the target user. For example, hackers use social media, dating apps and WhatsApp messages to try to convince affected users to install TestFlight and the malicious app on their iPhone devices.
This is an active risk so iPhone users are advised to stay on top of any signs of attack before it’s too late.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











