Cybersecurity specialists report the detection of a new remote access Trojan (RAT) that, in addition to including the functions of this malware variant, also has spyware and ransomware capabilities.
Borat RAT, dubbed after the character played by comedian Sacha Baron Cohen, is sold to all kinds of threat actors through hacking forums on the dark web, according to experts from cybersecurity firm Cyble Research.
The researchers mention that the Trojan is packaged with a constructor, function modules, and a server certificate. The malware has extensive capabilities, including keylogger function, ransomware encryption and decryption component, plus an option feature for attackers to create their own ransom notes and a function for deploying denial of service (DoS) attacks.
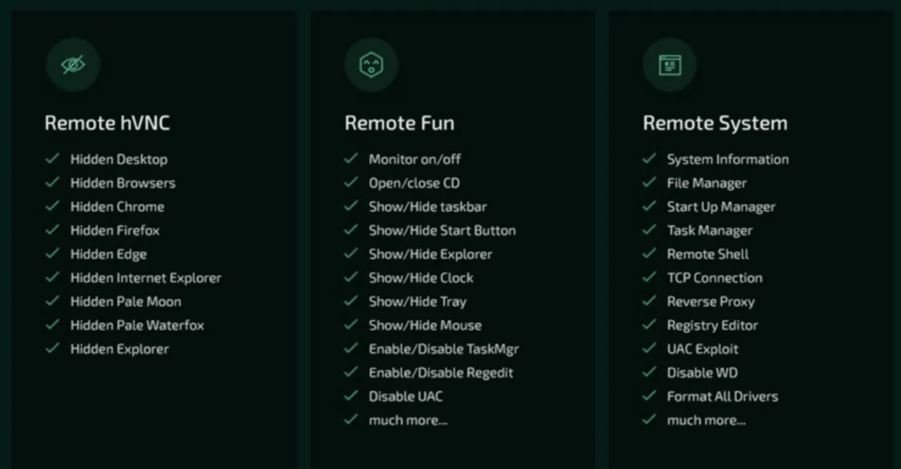
In addition, Borat RAT can remotely record audio from an affected machine by taking control of the microphone, capturing webcam images and other remote control functions, including mouse/keyboard hijacking, screenshots, modifying settings and deleting files.
After installation, the malware will start collecting data from the affected environment and then sending it to a C&C server under the control of the attackers. Apparently, Borat RAT focuses on browser information, including cookies, browsing histories, bookmarks, favorites, and users’ credentials. Tools like Chrome, Microsoft Edge, and Discord tokens are especially exposed to this attack variant.
The researchers add that Borat can cause inconvenience to victims in many other ways, as it allows hackers to perform all sorts of annoying tasks such as playing audio, altering mouse settings, hiding the taskbar, manipulating a computer’s LED lights and even turning it off unexpectedly, although the main risk is its advanced functions, uncommon for a RAT tool.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











