A report by F5 Networks points to the detection of a critical vulnerability that would allow threat actors with access to an exposed network to execute arbitrary commands, deploy file actions, and disable services on BIG-IP. Tracked as CVE-2022-1388, the flaw received a score of 9.8/10 according to the Common Vulnerability Scoring System (CVSS) and its exploitation could prove critical.
In total, the company fixed 17 severe vulnerabilities, many of which could result in severe compromise of the affected systems.
The bug resides in the iControl REST component and would allow malicious hackers to send requests capable of evading iControl REST authentication on BIG-IP products. The report was taken up by the Cybersecurity and Infrastructure Security Agency (CISA).

Among the affected products are:
- BIG-IP between v16.1.0 and v16.1.2
- BIG-IP between v15.1.0 and v15.1.5
- BIG-IP between v14.1.0 and v14.1.4
- BIG-IP between v13.1.0 and v13.1.4
- BIG-IP between v12.1.0 and v12.1.6
- BIG-IP between v11.6.1 and v11.6.5
The company released the corrected versions v17.0.0, v16.1.2.2, v15.1.5.1, v14.1.4.6 and v13.1.5. The derived versions of 12.x and 11.x will not receive updates, as F5 considers that they have reached the end of their useful life; on the other hand. BIG-IQ Centralized Management, F5OS-A, F5OS-C and Traffic SDC are not affected by the flaw.
For deployments that cannot be updated immediately, F5 listed a number of workarounds to mitigate the risk of exploitation based on blocking any access to the iControl REST interface through its own IP addresses, as well as restricting access only for trusted users, and modifying the BIG-IP httpd configuration.
F5 BIG-IP devices are used in all kinds of organizations worldwide, so vulnerabilities like this represent severe security risks. As if that were not enough, corporate network administrators still do not pay enough attention to this attack vector, so attacks against these devices have increased significantly since 2020.
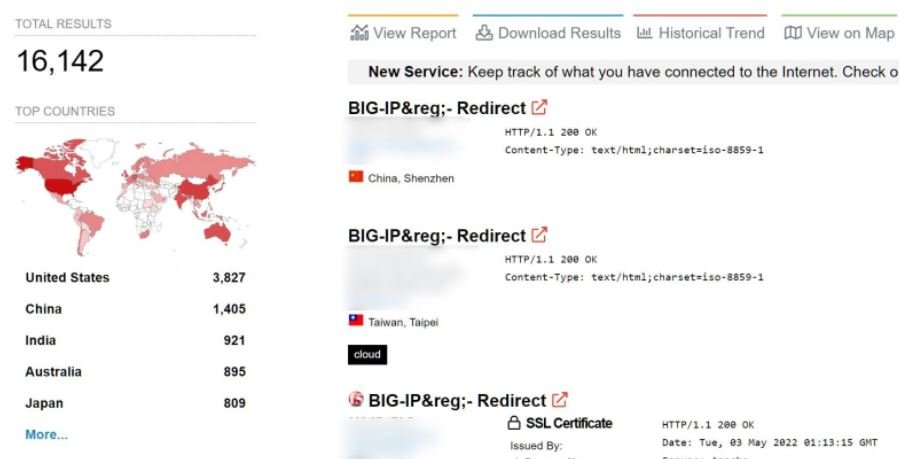
A quick scan at Shodan shows that there are nearly 16,200 F5 BIG-IP devices on display online, most in the United States, Australia, China, India and Japan.
Given the latent risk of exploitation, it is best for threat actors to address these flaws as soon as possible.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











