The U.S. Drug Enforcement Administration (DEA) reports that it has begun an investigation into alleged cyberattacks that would have compromised up to 16 databases of federal agencies. According to KrebsOnSecurity researchers, this incident could be related to a cybercriminal group whose members pose as law enforcement officers in order to access sensitive information.
A few days ago, investigators were alerted to a group of hackers with access to a username and password to the Law Enforcement Inquiry and Alerts (LEIA) system, which allows the search for information internally and in external database repositories, including data classified as “sensitive to law enforcement.” This report was shared with the Federal Bureau of Investigation (FBI) and the Department of Justice (DOJ). In total, LEIA enables federated search of 16 federal law enforcement databases in the U.S.
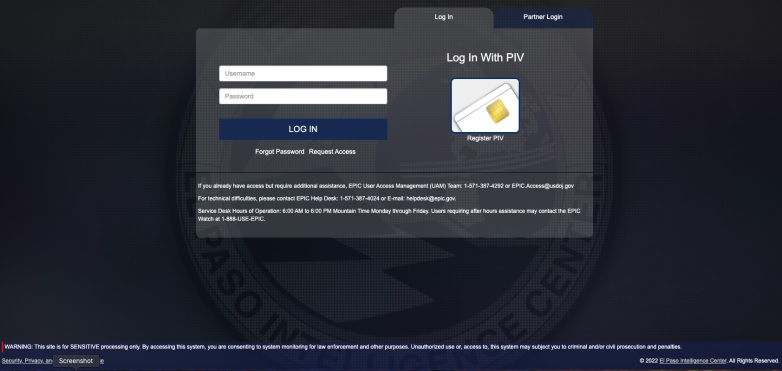
The report received by KerbsOnSecurity includes some screenshots indicating that hackers may have accessed the El Paso Intelligence Center (EPIC), one of the databases accessible from LEIA. In this database, threat actors would have searched for all kinds of records on seized assets, including cars, boats, weapons and even drones.
Strangely, this information was reported to KerbsOnSecurity by “KT”, administrator of an alleged online cybercriminal community known as Doxbin. This same threat actor has been identified as the leader of Lapsus$, a hacking group that recently carried out high-profile attacks against well-known companies such as Microsoft, NVIDIA and Samsung.
This hacker is also blamed for operating a service that offers fake Emergency Data Requests (EDR), using compromised email accounts from law enforcement agencies to ask tech companies for access to their users’ confidential information posing as police officers.
Although this activity has been linked to some alleged members of Lapsus$, at the moment it is unknown exactly who is behind these attacks, and even the possibility of a hacking group sponsored by national states is still being considered. DEA will continue to investigate the reports, so it only remains to wait for new details to be officially announced.
To learn more about information security risks, malware variants, vulnerabilities and information technologies, feel free to access the International Institute of Cyber Security (IICS) websites.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











