Cybersecurity specialists from AT&T Alien Labs report the detection of an Internet of Things (IoT) malware variant targeting content management systems (CMS), web servers, and Android devices. This malware would have been developed by the hacking group Keksec, formed in 2016 and which integrates various botnets.
The malware, identified as EnemyBot, targets services such as VMware Workspace ONE, Adobe ColdFusion, and WordPress, as well as some IoT and Android devices. EnemyBot has been deployed at an astonishing speed thanks to the exploitation of known security flaws.
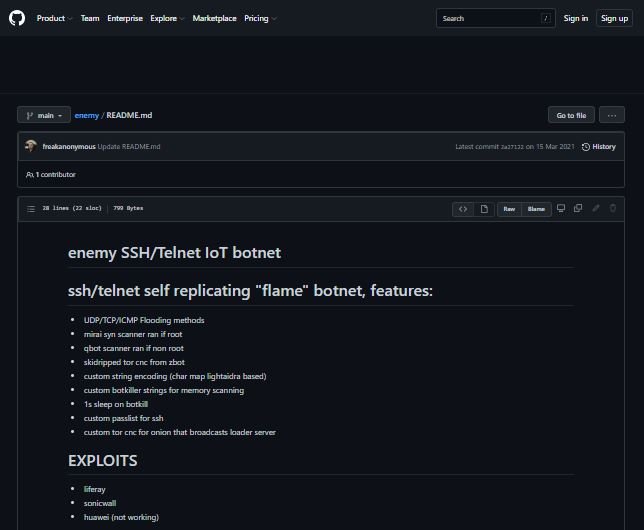
This new malware was developed from the source code used by other botnets, including Mirai, Qbot, and Zbot. Hackers use EnemyBot to target Linux systems and IoT devices.
A closer look
According to the report, malware is divided into four main sections:
- A Python script ‘cc7.py’, used to download all dependencies and compile malware on different operating system architectures (x86, ARM, macOS, OpenBSD, PowerPC, MIPS). After compilation, a batch file “update.sh” is created for malware propagation
- The main source code, which includes all the functions of EnemyBot, and incorporates the source code of the other botnets
- A hide.c segment that is manually compiled and executed to encode/decode malware strings
- A command and control (C&C) component to receive vital actions and payloads from hackers
The malware also features a feature for scanning vulnerable IP addresses and an “adb_infect” feature, which abuses the Android Debug Bridge feature for mobile device compromise.
Among the failures exploited in this campaign are:
- CVE-2021-44228 and CVE-2021-45046, also known as Log4Shell
- CVE-2022-1388, a vulnerability in F5 BIG IP devices
- CVE-2022-25075, TOTOLink A3000RU routers fail
- CVE-2021-35064, flaw at Kramer VIAWare
While researchers believe this campaign is in its early stages, the constant updating that malware receives and the possibility of exploiting multiple vulnerabilities would allow hackers to deploy massive campaigns soon.
Feel free to access the International Institute of Cyber Security (IICS) websites to learn more about information security risks, malware variants, vulnerabilities, and information technologies.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











