Although data stolen from Cisco have been released by a cybercriminals gang, the networking behemoth stands by its original evaluation of the event and claims there is no effect on its company.
On August 10, Cisco acknowledged that it had discovered a security issue on May 24. The revelation was brought on by the Yanluowang ransomware organization, which published a list of documents it claimed to have stolen from Cisco and claimed to have taken gigabytes of data.
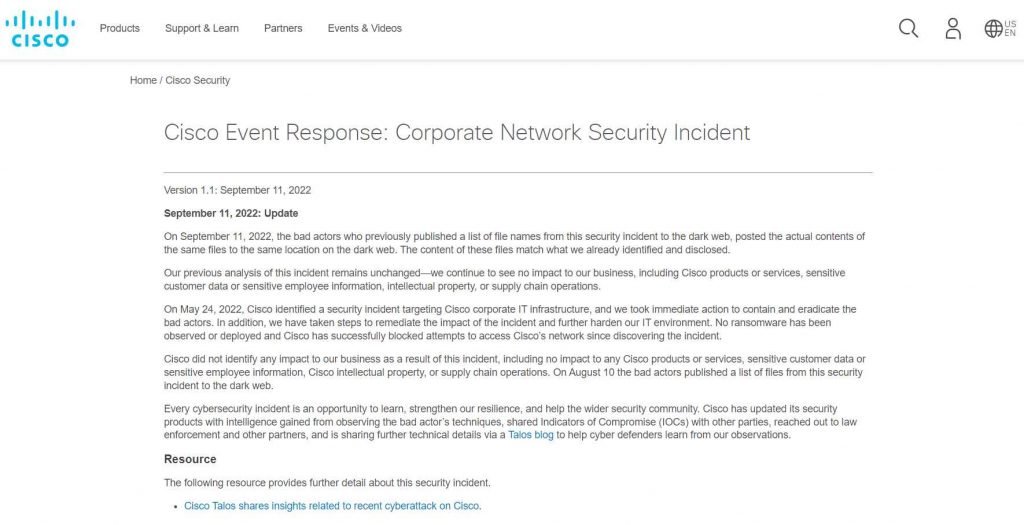
The actual data that were stolen from Cisco have now been made public by the cybercriminals, and Cisco has acknowledged that it belonged to the company.
The business claimed that one of its staff was the target of the intruder. It said that the only information taken was employee login information from Active Directory and non-sensitive documents saved in a Box account.
After obtaining the employee’s credentials, the attackers employed social engineering techniques to surpass multi-factor authentication (MFA) and get more data.
After gaining initial access, they began installing post-exploitation and remote access tools, increased their level of access, installed backdoors, and moved laterally throughout the network.
Although the malicious actors did email Cisco executives after the breach was detected, no ransom demands or explicit threats were made in the intrusion. File-encrypting ransomware was not used.
Cisco stated in a Sunday update that “the content of this leak matches what we have detected and released.” We continue to notice no effect on our company, including Cisco goods or services, confidential customer information or confidential employee data, intellectual property, or supply chain activities, which is consistent with our earlier examination of this event.
In August, Cisco identified the perpetrator as an initial access broker with connections to the Lapsus$ gang, the Yanluowang ransomware organization, and the Russia-linked threat actor UNC2447.

Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.











