Microsoft has acknowledged that it is aware of two zero-day vulnerabilities in Exchange Server that have been used in deliberate attacks. The tech behemoth is developing fixes.
Two new Microsoft Exchange zero-day flaws have been used in attacks, according to Vietnam-based cybersecurity firm GTSC. The company thinks a Chinese threat organization was behind the attacks, which targeted key infrastructure and were first observed in August.
The GTSC did note that the threat actor’s post-exploitation activities included the implementation of backdoors, lateral movement, and the distribution of malware.
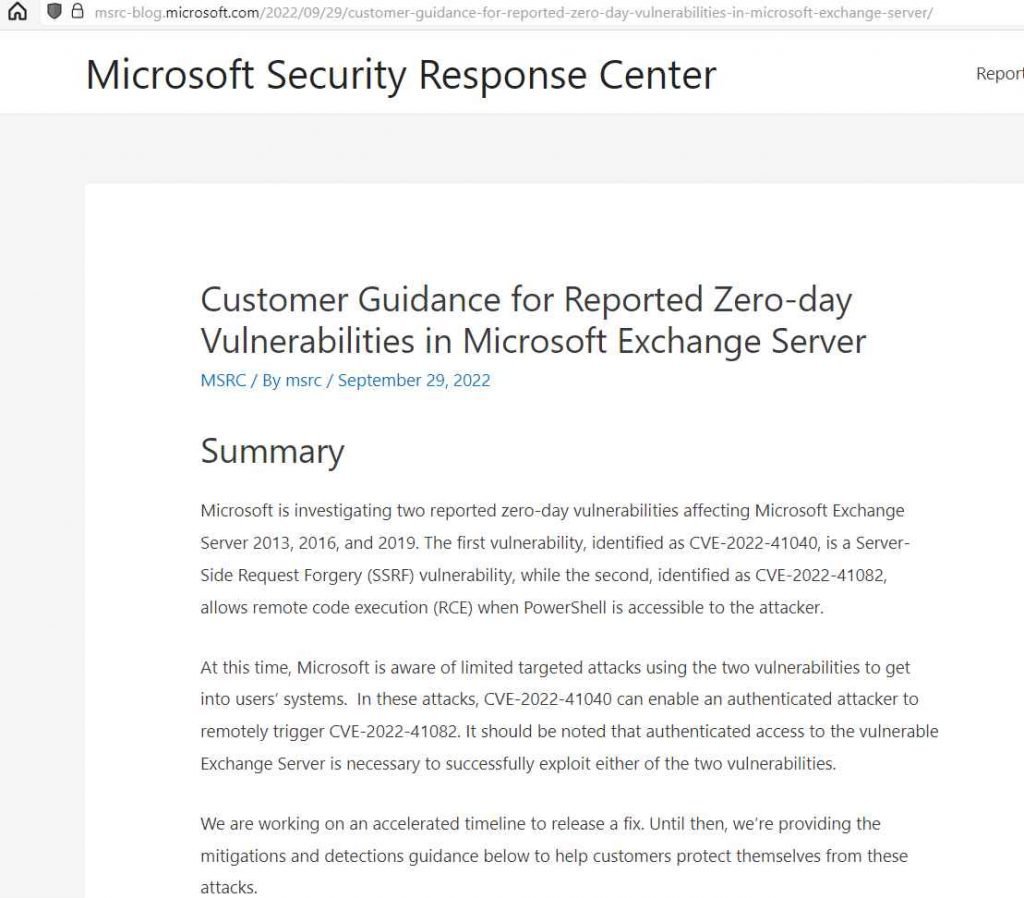
Through Trend Micro’s Zero Day Initiative, Microsoft was informed of the vulnerabilities (ZDI). Microsoft has already announced on its blog that it is looking into two alleged zero-day vulnerabilities.
The IT company claims that one of the issues is a remote code execution flaw (CVE-2022-41082) and the other is a server-side request forgery (SSRF) flaw. It has been discovered that the security flaws affect Exchange Server 2013, 2016, and 2019.
Microsoft is now aware of a small number of targeted attacks leveraging the two vulnerabilities to compromise customers’ PCs. These attacks allow an authorized adversary to remotely activate CVE-2022-41082 due to CVE-2022-41040. It should be noted that in order to properly exploit any of the two vulnerabilities, authorized access to the exposed Exchange Server is required, according to Microsoft.
The business is attempting to fix the vulnerabilities on a hurried schedule. In the meanwhile, it has offered comprehensive instructions on how exploitation might be avoided. According to Microsoft, their security software should be able to identify any post-exploitation malware and related behavior. Customers of Microsoft Exchange Online do not need to take any action.

Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.











