The message encryption system employed by Microsoft in Office 365 has a system vulnerabilities, according to a warning from the Finnish cybersecurity company WithSecure. According to WithSecure’s alert, the Office 365 Message Encryption (OME) security technique is defective, which makes it possible for the Microsoft 365 security vulnerability to be used to infer message contents.
This technique is used to send and receive encrypted emails between internal and external users without revealing any information about their correspondence.
Due to the weakness, malicious third parties may get access and be able to decrypt encrypted emails, revealing private user communications. The secrecy of the communications is compromised since the ECB divulges their structural information.
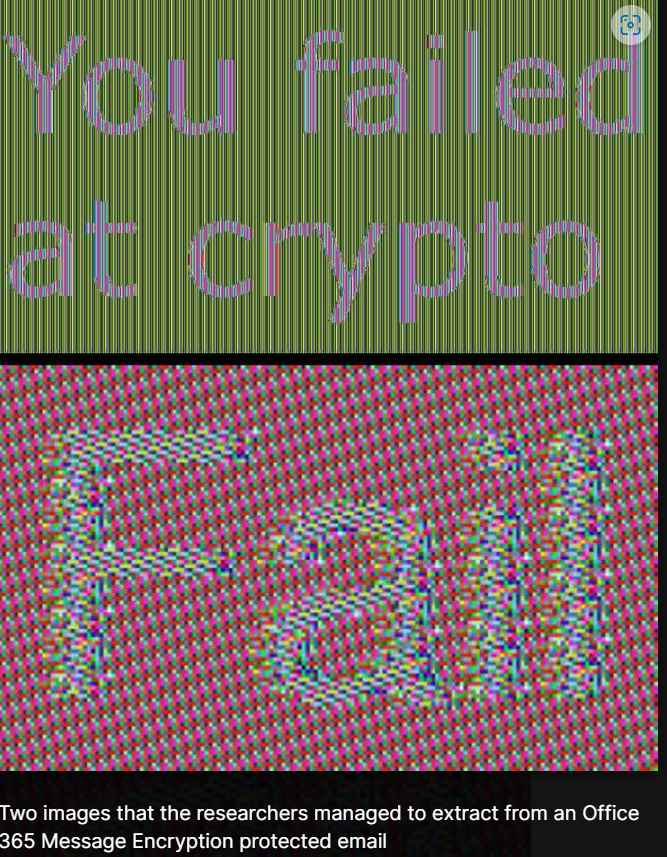
WithSecure was able to decrypt an image’s AES-encrypted data during analysis. The underlying issue, according to researchers, is the ECB mode, not AES. When WithSecure alerted Microsoft, the business said the report didn’t fulfill the criteria for security servicing and doesn’t qualify as a breach, according to information given by WithSecure.
“Neither a breach nor a notification were deemed to fulfill the standards for security servicing. Since there was no code modification, there was no CVE for this report.
Microsoft
Even though WithSecure demonstrated that there was a chance of exploitation, it also cited NIST’s response, in which the organization acknowledged that the ECB mode was in fact defective. However, until Microsoft provides a remedy or a better alternative is available, users should exercise caution and companies employing OME for email encryption should avoid adopting it as the exclusive source of email secrecy.

He is a well-known expert in mobile security and malware analysis. He studied Computer Science at NYU and started working as a cyber security analyst in 2003. He is actively working as an anti-malware expert. He also worked for security companies like Kaspersky Lab. His everyday job includes researching about new malware and cyber security incidents. Also he has deep level of knowledge in mobile security and mobile vulnerabilities.











