Any contemporary software company must have environments, procedures, and systems for continuous integration and continuous delivery. They transport the code written at an engineer’s workstation to the production environment. The engineering ecosystem has been significantly reformed as a result of the proliferation of CI/CD systems and procedures, which has also been accompanied by the growth of the DevOps discipline and microservice designs.
The technological stack is more diversified, both in terms of the programming languages that are used and the technologies and frameworks that are acquired later on in the development process (e.g. GitOps, K8s).
The adoption of new programming languages and frameworks is happening at a far faster rate and with less substantial technical hurdles.
Automation and methods known as Infrastructure as Code (IaC) are becoming more and more widespread usage.
Third parties, both in the form of external providers and as dependents in code, have become an important component of any CI/CD ecosystem. The incorporation of a new service often requires little more than the addition of one to two lines of code.
These properties make it possible to distribute software in a more rapid, flexible, and diversified manner. However, in doing so, they have also remodeled the attack surface, creating a plethora of new paths and openings via which attackers might gain access.
In today’s world, adversaries of all levels of expertise are moving their focus to CI/CD because they have realized that CI/CD services offer an effective way to accessing an organization’s most valuable assets. The industry is experiencing a considerable surge in the number of events and attack vectors that are concentrating on exploiting holes in the CI/CD ecosystem, as well as an increase in their frequency and volume.
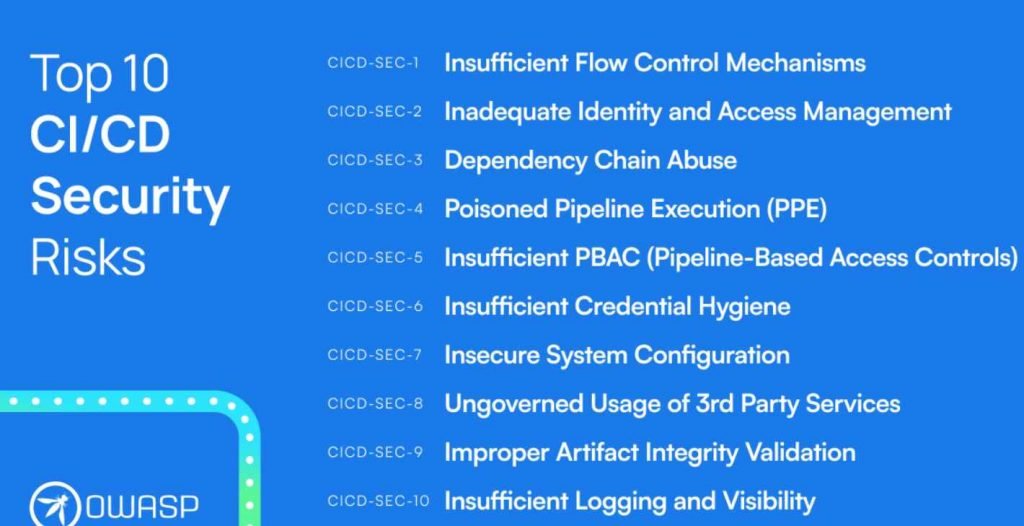
The “Top 10 CI/CD Security Risks” framework has been officially adopted as an OWASP project and given the name “OWASP Top 10 CI/CD Security Risks”!
The Open Web Application Security Project (OWASP), and more specifically the “Top 10 Web Application Security Risks” framework, has been a significant factor in the development of the application security industry. This has been true in terms of how methodologies and thought patterns have been formed, as well as how the landscape of Web Application Security technologies has been shaped.
To this day, OWASP continues to play a pivotal role in shaping the trajectory of the Application Security (AppSec) domain through an incredible community and infrastructure that enables Application Security (AppSec) practitioners all over the world to build, share, and spread knowledge about anything related to Application Security (AppSec).
The project known as the “Top 10 CI/CD Security Risks.”
This project guides defenders through the process of identifying target areas for the purpose of safeguarding their CI/CD ecosystem. It is the product of considerable study into attack vectors linked with CI/CD, as well as the investigation of high-profile breaches and security weaknesses in existing systems.
CICD-SEC-1: Insufficient Flow Control Mechanisms
CICD-SEC-2: Inadequate Identity and Access Management
CICD-SEC-3: Dependency Chain Abuse
CICD-SEC-4: Poisoned Pipeline Execution (PPE)
CICD-SEC-5: Insufficient PBAC (Pipeline-Based Access Controls)
CICD-SEC-6: Insufficient Credential Hygiene
CICD-SEC-7: Insecure System Configuration
CICD-SEC-8: Ungoverned Usage of 3rd Party Services
CICD-SEC-9: Improper Artifact Integrity Validation
CICD-SEC-10: Insufficient Logging and Visibility

Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.











