Following the release of an emergency patch by Fortinet to address significant security flaws in the FortiOS SSL-VPN product. Citrix has just just issued yet another critical security update for its Citrix ADC and Citrix Gateway products.
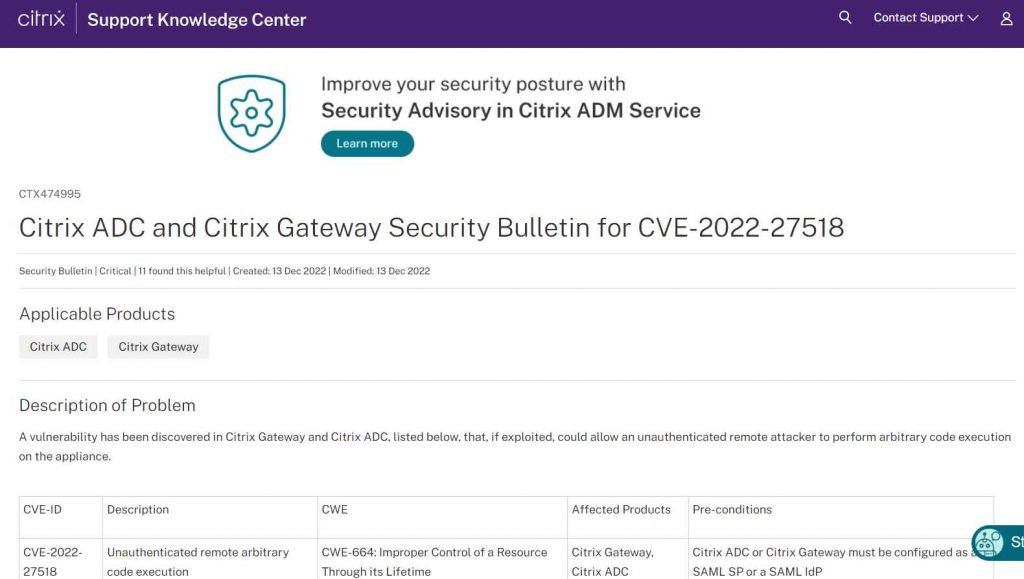
The company has patched a critical zero-day vulnerability that has been identified as CVE-2022- 27518. This threat affects the following versions of Citrix ADC and Citrix Gateway: 12.1 (including FIPS and NDcPP) and 13.0 before 13.0-58.32 of Citrix ADC and Citrix Gateway; in order to be vulnerable, both components must be configured with a SAML SP or IdP configuration. Because of this newly discovered vulnerability, an unauthenticated attacker is now able to remotely execute instructions on susceptible devices and take control of such devices. Citrix said that state-sponsored hackers routinely exploit the vulnerability in order to get access to business networks. Customers that are using an impacted build with a SAML SP or IdP configuration are strongly encouraged to install the suggested builds as soon as possible due to the serious nature of this issue (CTX474995). There is currently no solution or workaround available for this issue. This vulnerability has been exploited in a limited number of targeted assaults in the wild, as far as we are aware.
CISA recommends users and administrators to check Citrix’s security advisory and apply the appropriate upgrades. This is in response to Citrix’s strong recommendation that administrators implement security updates in response to this significant zero-day vulnerability. Additionally, the Center for Internet Security Analysis (CISA) strongly recommends that organizations read the National Security Agency’s advisory titled APT5: Citrix ADC Threat Hunting Guidance. This document provides detection and mitigation guidance against tools used by malicious actors to target vulnerable Citrix ADC systems.
“Citrix® Application Delivery ControllerTM (ADCTM) installations have been shown to be vulnerable to the threat posed by APT5, which has successfully proved its capabilities (“Citrix ADCs”). By avoiding the typical authentication measures, unauthorized access to the companies that are the focus of the attack may be made possible via the targeting of Citrix ADCs “according to the alert issued by the NSA today.
It is widely assumed that APT5 is a Chinese state-sponsored hacking gang. This group is notorious for exploiting zero-day vulnerabilities in VPN equipment in order to get initial access and steal sensitive data.
Affected products
The following versions of Citrix ADC and Citrix Gateway are susceptible to attack due to the vulnerability:
Citrix Access Delivery Controller and Citrix Gateway 13.0 before 13.0-58.32
Citrix Application Delivery Controller 12.1 and Citrix Gateway 12.1 prior to 12.1-65.25
Citrix ADC 12.1-FIPS formerly known as 12.1-55.291
Until 12.1-55.291, the Citrix ADC version 12.1-NDcPP
Only in the case when the appliances are set up to function as a SAML SP (SAML service provider) or SAML IdP are the versions listed above affected (SAML identity provider).
By searching for the following commands in the ns.conf file, an administrator may establish whether the Citrix ADC or Citrix Gateway under their administration is set up to function as a SAML SP or a SAML IdP.
add authentication samlAction
add authentication samlIdPProfile
The administrator should immediately apply the update if any of the commands are found in the ns.conf file and they are running a version of the software that is impacted.
Citrix urgently advises administrators to install security updates for Citrix ADC and Gateway due to a “Critical” zero-day vulnerability (CVE-2022-27518) that is being actively exploited by state-sponsored hackers to access business networks.

Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.











