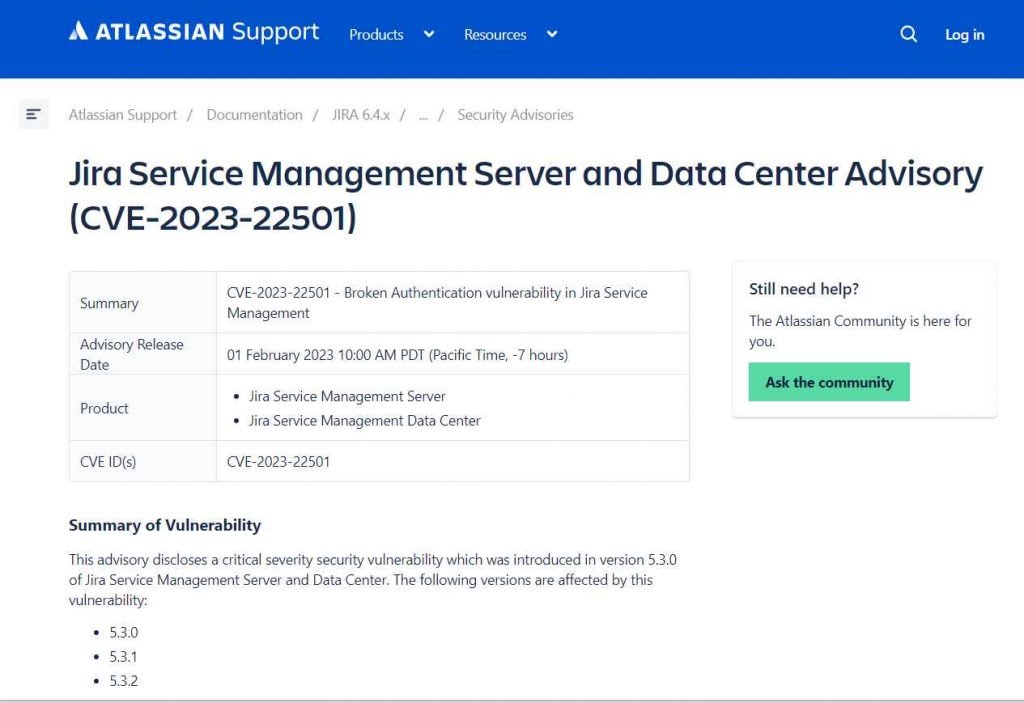
Jira Service Management Server and Data Center include a significant vulnerability that has been tracked as CVE-2023-22501 (CVSS score: 9.4) and has been patched by Atlassian. Under some conditions, an attacker might use this vulnerability to assume the identity of another user and obtain unauthorized access to other Jira Service Management instances.
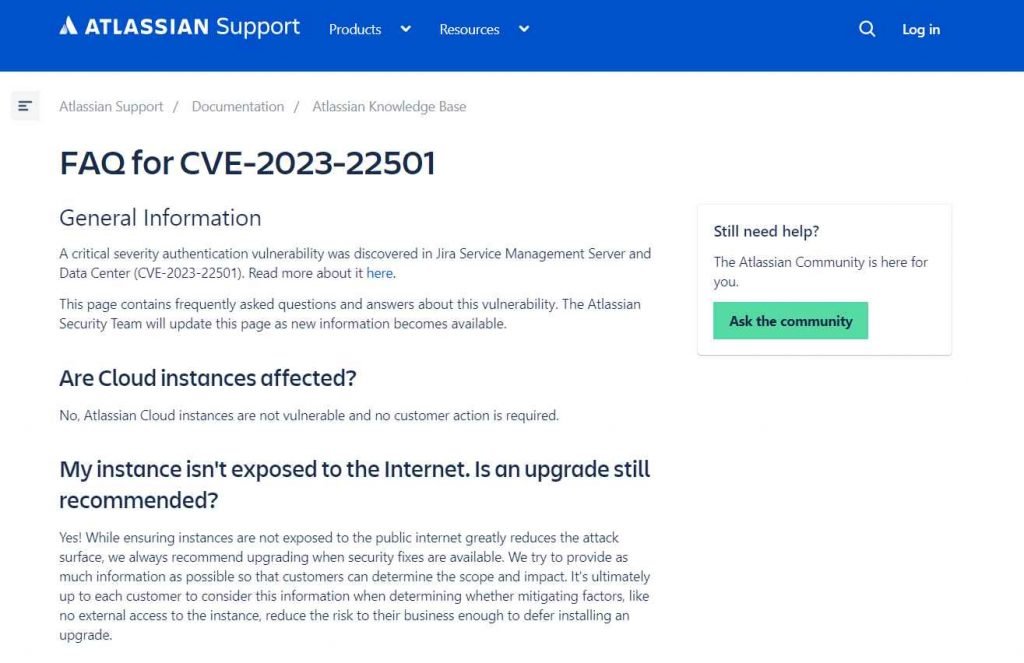
Users that visit their Jira site via an atlassian.net domain are not vulnerable to the issue, as it was pointed out in the alert. If your Jira site is hosted by Atlassian, then you will not be impacted. atlassian.net domain, it is hosted by Atlassian, which means that you are not vulnerable to the security issue.
Jira sites that are hosted in the cloud and use an atlassian[.]net domain are not vulnerable to the issue, according to Atlassian, and users do not need to take any preventative measures in this scenario.
According to Atlassian, the vulnerability affects versions 5.3.0 through 5.5.0, and criminals have the potential to get “access to a Jira Service Management instance under certain conditions.”
“An attacker might acquire access to signup tokens provided to users with accounts that had never been registered into if they had write access to a User Directory with outgoing email enabled on a Jira Service Management server,”
It is possible to use it to specifically target bot accounts because of the frequent interactions they have with other users and the increased likelihood that they will be included in Jira issues or requests or receive emails containing a “View Request” link. Either of these conditions is required in order to acquire signup tokens.
This major vulnerability that allowed an attacker to impersonate another user and get access to a Jira Service Management instance been addressed by Atlassian. The vulnerability was present in the Jira Service Management Server and Data Center.
Atlassian has provided updates that solve the problem and urges administrators to upgrade to versions 5.3.3, 5.4.2, 5.5.1, and 5.6.0 or later. These updates may be found on the Atlassian website.
In the event that the update cannot be implemented immediately, the vendor has made available a workaround in the form of a JAR file that can be used to upgrade the “servicedesk-variable-substitution-plugin” manually. The procedures required to do this are as follows:
Download the JAR file that is specific to the version from the advisory.
Stop Jira
The JAR file should be copied into the Jira home directory (which is located at “Jira Home>/plugins/installed-plugins” for servers and “Jira Shared/plugins/installed-plugins” for data centers).
Start the service all over again.
Both the Crowd Server and Data Center, the company’s identity management platform, and the Bitbucket Server and Data Center, a self-managed solution that provides source code collaboration for professional teams, were found to have vulnerabilities of critical severity in November of 2022. These vulnerabilities were addressed by the company.
A significant command injection vulnerability exists in the Bitbucket source code repository hosting service. This vulnerability is tracked under the CVE identifier CVE-2022-43781.

Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.











