An adversary may circumvent encryption for some communications by exploiting a flaw in the widespread 802.11 protocol, which enables them to do so. The university researchers that made the discovery claim that the flaw enables an adversary to “trick access points into leaking frames in plaintext, or encrypted using the group or an all-zero key.”
Due to the fact that it is a flaw in the Wi-Fi protocol, it impacts more than one implementation. A ground-breaking academic paper with the provocative title “Framing Frames: Bypassing Wi-Fi Encryption by Manipulating Transmission Queues” was made available to the public on March 27, 2023. This document revealed flaws in the 802.11 Wi-Fi standard. Because of these vulnerabilities, an attacker could be able to impersonate a targeted wireless client and reroute frames that are already in the transmit queues of an access point to a device that the attacker controls. In this post, we will analyze the workings of this opportunistic attack and investigate the many preventative measures that may be taken to protect your network from this danger.
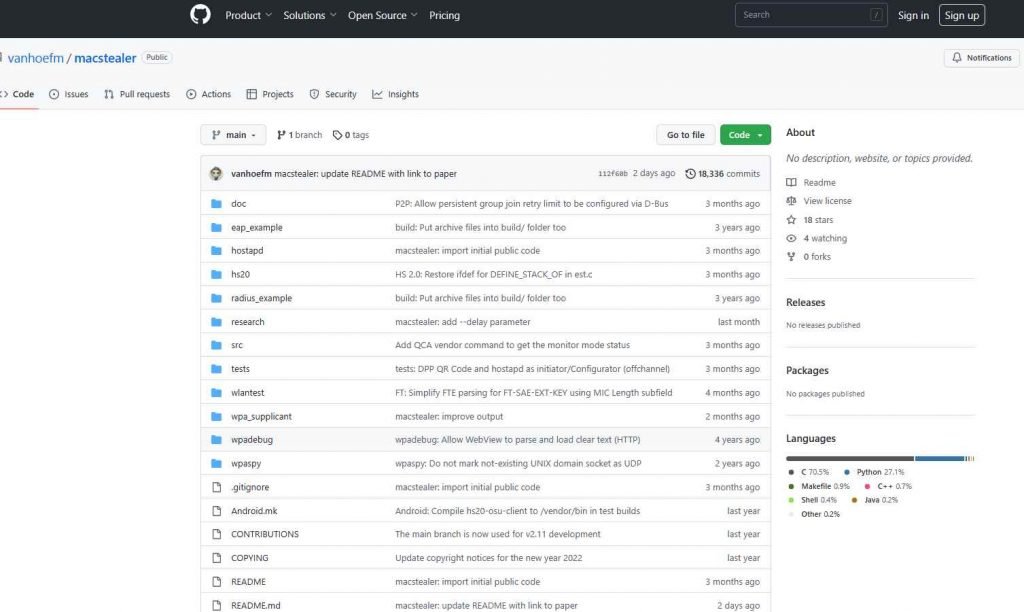
The attack, which has been given the name “MacStealer,” is directed against Wi-Fi networks that include hostile insiders and takes advantage of client isolation bypasses (CVE-2022-47522). Even if clients are unable to communicate with one another, it is able to intercept communication at the MAC layer. Wi-Fi networks that use client isolation, Dynamic ARP inspection (DAI), and other mechanisms meant to prevent clients from attacking one another are susceptible to this issue.
The first company to recognize the flaw was Cisco, which said that the attacks described in the research article might be effective against Cisco Wireless Access Point devices and Cisco Meraki products with wireless capabilities. Cisco was the first firm to admit the issue.

The client authentication and packet routing processes in Wi-Fi networks function independently of one another, which is the root cause of the security hole known as CVE-2022-47522. The usage of passwords, users, 802.1X IDs, and/or certificates is required for authentication, although MAC addresses are what determine how packets are routed. This inconsistency may be exploited by a malicious insider who disconnects a victim from the network and then reconnects to it using the victim’s MAC address and the attacker’s credentials. As a consequence of this, any packets that are still on their way to the victim, such as data from a website, will instead be received by the attacker.
The following are the three basic stages of this attack:

The attacker will wait for the victim to connect to a susceptible Access Point (AP), at which point the attacker will submit a request to an internet server. For example, the attacker may send an HTTP request to a website that only displays plaintext.
Steal the Identifying Information of the Victim: The perpetrator of the attack removes the victim’s network connection before the AP has a chance to process the server’s response. After that, the attacker creates a fake version of the victim’s MAC address and logs in to the network using their own credentials.
Intercept the Response: At this step, the access point (AP) pairs the attacker’s encryption keys with the victim’s MAC address. This gives the attacker the ability to intercept any pending traffic that is destined for the victim.
It is essential to keep in mind that the communication that is being intercepted may be secured by higher-layer encryption, such as that provided by TLS and HTTPS. Therefore, regardless of whether or not a higher-layer encryption is being used, the IP address that a victim is talking with may still be discovered by this approach. This, in turn, exposes the websites that a victim is viewing, which, on its own, might be considered sensitive information.
All Corporate WPA1, WPA2, and WPA3 networks are vulnerable to the attack in exactly the same way. This is due to the fact that the attack does not take use of any cryptographic features of Wi-Fi; rather, it takes advantage of the way in which a network decides to which client packets should be transmitted, sometimes known as routing.
To summarize, the attack described in the “Framing Frames” study is a worrying vulnerability that presents the possibility of adversaries being able to intercept and perhaps read sensitive information that is being carried across Wi-Fi networks. It is essential for businesses to take all of the required steps, such as implementing strong security measures and using mitigations that have been advised, in order to guarantee the safety and security of their networks.
Using 802.1X authentication and RADIUS extensions are two methods that may be utilized to stop MAC address theft. Safeguarding the MAC address of the gateway, putting in place Managed Frame Protection (802.11w), and making use of virtual local area networks (VLANs) are all viable mitigations. The use of policy enforcement techniques using a system such as Cisco Identity Services Engine (ISE), which may limit network access by utilizing Cisco TrustSec or Software Defined Access (SDA) technologies, is something that Cisco advises its customers to do. It is also recommended by Cisco to implement transport layer security in order to encrypt data while it is in transit if it is practicable to do so. This would prevent an attacker from using the data they have collected.

Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.











