Rules_oci, an open-sourced Bazel plugin (“ruleset”) that makes it easier and more secure to create container images using Bazel, has been made generally available by Google. It provides support for both the container community and container image security. Bazel maintains dependencies and caches them according to their integrity hash, making it ideally suited to provide supply chain guarantees based on the Trust-on-First-Use concept. Building widely used Distroless base images for Docker is one way Google makes use of Bazel.
Distroless is a set of basic images with the bare minimum that increase supply-chain security. They adhere to best practices followed by Google and other big organizations that have been using containers in production for many years. They limit the content of your runtime container to only what is required for your app. Utilizing basic base images eases the cost of handling risks related to supply chain concerns such as licensing, governance, and security vulnerabilities.
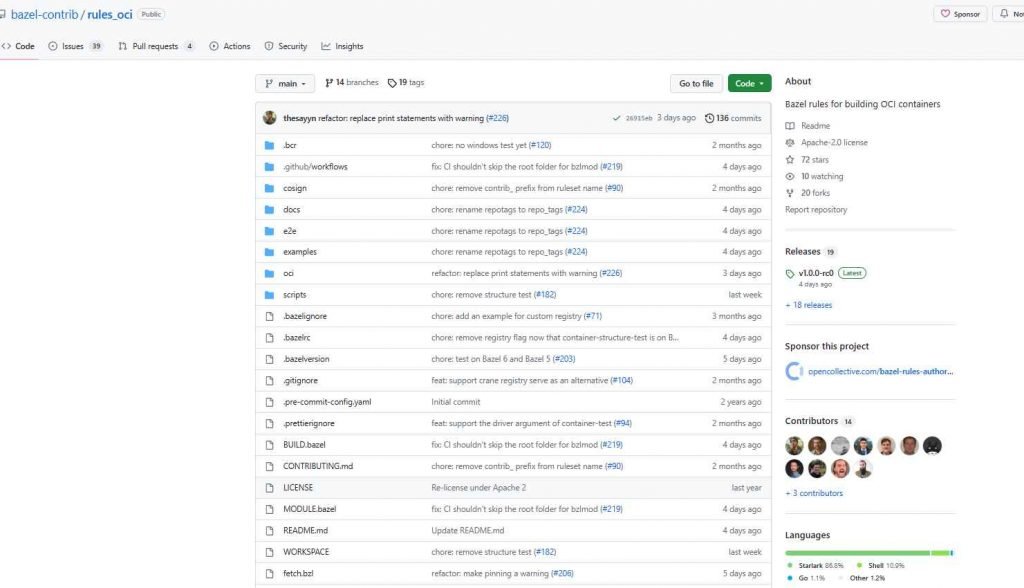
In the past, rules_docker enabled creating container images; however, it is now in maintenance mode. For a number of reasons, the new ruleset, termed rules_oci, is more appropriate for Distroless and the majority of Bazel container builds.
There are currently several container runtimes and image formats as a result of the Open Container Initiative standard. Rules_oci is not dependent on a machine’s currently running Docker daemon.
Before great container manipulation tools like Crane, Skopeo, and Zot existed, rules_docker was developed. Rules_oci may avoid developing or maintaining any Bazel-specific tools by simply relying on trustworthy third-party toolchains.
Rules_oci is significantly easier to maintain than Rules_docker since it doesn’t include any language-specific rules. Additionally, it stays away from the drawbacks of outdated dependency on other language rule sets. Rules_oci also has several more fantastic features that are worth mentioning. For instance, it enhances caching and makes usage of a private registry transparent by using Bazel’s downloader to collect layers from a distant registry. Targeting systems like ARM-based servers is made easier by multi-architecture images, which also enable Windows Containers. Users may use code signing to ensure that any container images they use were developed by the developer who signed them and were not altered along the way (for example, by a person-in-the-middle attack). This is an excellent moment to give rules_oci a try if you already use rules_docker or are thinking about utilizing Bazel to construct your containers.

Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.











