According to a report published by SentinelLabs on Thursday, a Brazilian hacking crew targeted users of more than 30 Portuguese financial institutions earlier this year in a campaign that provides the latest example of powerful, financially motivated hackers in Brazil targeting targets outside of the country’s borders. The campaign was part of a campaign that targeted users of more than 30 financial institutions in Portugal.
Researchers Aleksandar Milenkoski and Tom Hegel said in a report that was released on Thursday that the ongoing campaign, which has been given the codename “Operation Magalenha,” initially relied on cloud service providers such as DigitalOcean and Dropbox. However, as a result of these companies tightening rules on how their services can be used, the operation has pivoted to the Russia-based web hosting provider TimeWeb. The operation started at the beginning of this year, but the majority of the assaults were carried out in the most recent month.
Hacking groups based in Brazil that were becoming increasingly sophisticated carried out operations together with malware developers based in other countries, including Eastern Europe and Russia. This is how the Brazilian malware ecosystem first caught the attention of the information security industry nearly a decade ago. Researchers from Kaspersky in the year 2020 labeled a grouping of four banking trojans as “Tetrade.” This grouping originated in Brazil, which continues to be the hub of the most powerful financially-focused malware.
The ongoing existence of the Brazilian cybercriminal underground is shown by Operation Magalenha, as is the steadily increasing danger presented by the threat players operating inside it. According to what Milenkoski and Hegel wrote in their research, these organizations have “a consistent capacity to update their malware arsenal and tactics, which allows them to remain effective in their campaigns.”
Phishing emails that are purporting to originate from Energias de Portugal (EDP) and the Portuguese Tax and Customs Authority (AT), as well as social engineering and malicious websites that resemble these institutions, are some of the tactics that the attackers employ to spread their malware to their targets. Other methods include social engineering.
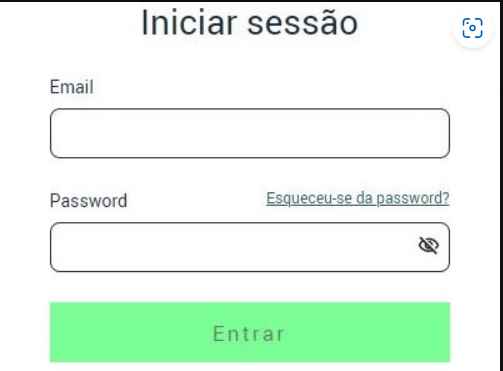
The infection starts with the execution of an obfuscated VB script, which then retrieves and runs a malware loader. After a five-second wait, the malware loader then installs two different versions of the ‘PeepingTitle’ backdoor onto the machine of the victim. This is how the infection starts in all situations. The experts note that the objective of such scripts is to distract the users while malware is downloaded and to steal their EDP and AT credentials by leading them to the relevant phony portals. This is accomplished by redirecting the users to the fake websites.
PeepingTitle is a piece of malicious software that was built in Delphi and has a compilation date of April 2023. Sentinel Labs thinks that it was created by either a single individual or a team. The attackers drop two variations because they want to use one for recording the victim’s screen and the other for monitoring windows and the user’s interactions with those windows. This is why the attackers drop two variants.

After registering the target system and delivering reconnaissance information to the attackers, the second variation is also able to retrieve more payloads to steal. The virus searches for windows that match a predefined list of financial institutions, and when it discovers one, it begins logging all user input (including credentials) and sending it to the command and control server of the malicious actor. Screenshots may also be taken using PeepingTitle, processes on the host can be terminated, PeepingTitle’s monitoring interval settings can be changed on the fly, and it can stage payloads derived from executables or DLL files by utilizing Windows rundll32.
According to the researchers, Operation Magalenha is the most recent version of a larger group of financially driven hacking attempts that started in 2021. This larger group includes Operation Magalenha.
In its most recent incarnation, it grants the attacker power over infected PCs by relying on a pair of backdoors that must be launched at the same time. The backdoors, which have been given the name “PeepingTitle,” provide the attacker the ability to monitor window activity, capture screenshots without authorization, terminate processes, and install other malware, such as data exfiltration tools.
According to the researchers, “their ability to plan attacks in Portuguese and Spanish-speaking nations in Europe, Central, and Latin America suggests an understanding of the local financial landscape and a willingness to expend time and resources in developing targeted campaigns.”

Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.











