Attackers will have an easier time reading encrypted data if the Cisco ACI Multi-Site CloudSec encryption function of the Cisco Nexus 9000 Series switches is vulnerable to a serious issue. This weakness allows attackers to access encrypted traffic. The issue was identified as CVE-2023-20185 and has a CVSS score of 7.4.
This vulnerability, which is hidden deep inside the encryption capability of Cisco ACI Multi-Site CloudSec, exposes a possible backdoor for unauthorized, remote attackers to view and change intersite encrypted traffic on Cisco Nexus 9000 Series Fabric Switches when they are operating in ACI mode. This alarming breach in security was caused by a vulnerability in the way the CloudSec encryption function implemented the ciphers it employed, which was a fault in the system itself.This vulnerability might be exploited by an attacker who is stationed at an on-path point between the ACI sites. The attacker would do so by intercepting encrypted intersite communication. While the maze of internet may seem to be vast and impassable, it is not. The adversary may crack the encryption using powerful cryptanalytic methods, therefore getting unrestricted access to read or change the transmittal traffic between sites. This would allow the adversary to read or modify the data without being detected.
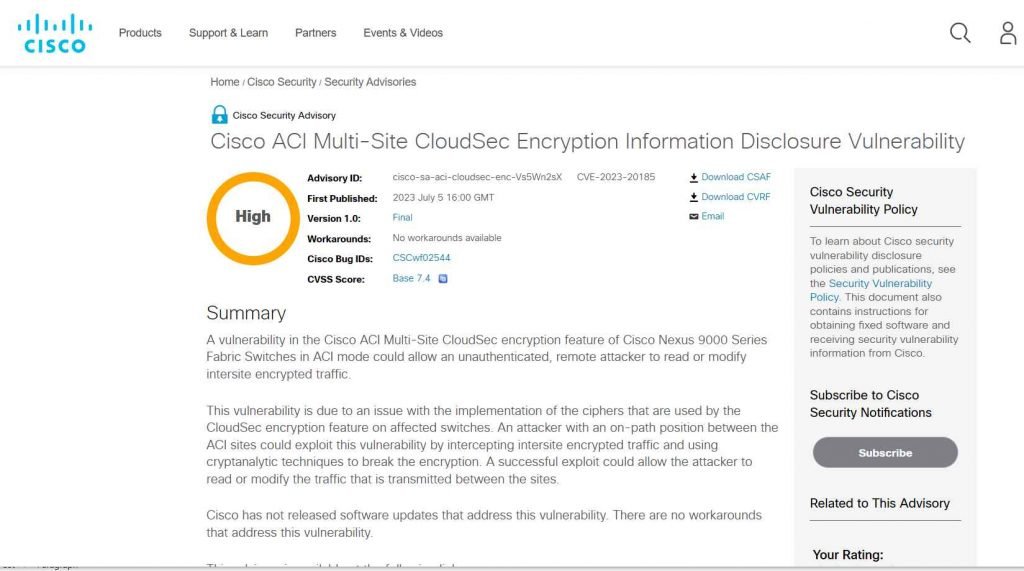
It is unfortunate to inform that, despite the frightening nature of this discovery, Cisco has not yet issued any software upgrades that address the major vulnerability. In addition, there are no alternate solutions or workarounds that have been discovered to combat this problem.
The security flaw known as CVE-2023-20185 is exclusive to Cisco Nexus 9000 Series Fabric Switches operating in ACI mode and using versions 14.0 or later. However, in order for these switches to be vulnerable, they must be a part of a Multi-Site topology that also has the CloudSec encryption function turned on. The use of Cisco Nexus 9332C or Cisco Nexus 9364C Fixed Spine Switches, or Cisco Nexus 9500 Spine Switches that are outfitted with a Cisco Nexus N9K-X9736C-FX Line Card, is now required in order to take use of this capability.
To check whether CloudSec encryption is enabled on an ACI site, open the Cisco Nexus Dashboard Orchestrator (NDO) and browse to Infrastructure > Site Connectivity > Configure > Sites > site-name > Inter-Site Connectivity.
Make sure that the “CloudSec Encryption” option is set to “Enabled.”
Simply entering the command “show cloudsec sa interface all” into the command line of your Cisco Nexus 9000 Series switch will allow you to determine whether or not the CloudSec encryption feature is active on your device.
The information that is generated will make it abundantly obvious what the “Operational Status” is as well as whether or not CloudSec encryption is enabled on any interface. Make sure that you follow these guidelines to the letter in order to get an accurate assessment of the encryption state of your switch.
Customers that are currently using the Cisco ACI Multi-Site CloudSec encryption function for the Cisco Nexus 9332C and Nexus 9364C Switches as well as the Cisco Nexus N9K-X9736C-FX Line Card are strongly encouraged to deactivate the capability.
Customers who are using the Cisco ACI Multi-Site CloudSec encryption function are strongly encouraged to deactivate it and get in touch with their support organization to examine other solutions since Cisco does not plan to release any software upgrades for the capability in the foreseeable future. There have been no public disclosures or known malicious usage of this vulnerability as of the time that this article was written, which provides a ray of optimism in light of these otherwise hopeless conditions.
According to Cisco (PSIRT), there are currently no active exploits of this vulnerability, and it was discovered during an internal assessment.
Affected are the Cisco Nexus 9000 Series Fabric Switches running versions 14.0 and later that are operating in ACI mode. Additionally, the switches must be a part of a Multi-Site topology.

Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.











