It is possible to remotely hack ATMs by taking advantage of a number of vulnerabilities that have been found in the ScrutisWeb ATM fleet monitoring software developed by the firm.Members of the Synack Red Team were the ones to uncover the vulnerabilities in the system, and the vendor addressed them in July 2023 with the release of ScrutisWeb version 2.1.38.ScrutisWeb enables businesses to monitor their banking or retail ATM fleets from inside a web browser, giving them the ability to immediately react to any issues that may arise. The solution enables users to remotely monitor hardware, restart or shut down a terminal, send and receive files, and alter data. It also enables users to transmit and receive files. It is important to note that a restaurant chain’s ATM fleet may also contain check deposit machines and payment terminals in certain cases.
Researchers from Synack discovered four distinct classes of vulnerabilities, each of which was given a CVE identification and given the numbers CVE-2023-33871, CVE-2023-38257, CVE-2023-35763, and CVE-2023-35189 respectively.
The following is an explanation of each of the four flaws:
CVE-2023-33871 is a directory traversal vulnerability that has a CVSS score of 7.5. This vulnerability might enable an unauthenticated user to directly access any file that is located outside of the server’s webroot directory.
CVE-2023-35189 is a vulnerability in the remote execution of code that has a CVSS score of 10.0. This vulnerability might enable an unauthenticated user to submit a malicious payload and subsequently execute it.
CVE-2023-35763 is a cryptographic vulnerability that has a CVSS score of 5.5. It is possible for an unauthenticated user to decode encrypted passwords into plaintext using this issue.
CVE-2023-38257 is an unsafe direct object reference vulnerability that has a CVSS score of 7.5. This vulnerability might enable an unauthenticated user to access profile information, such as user login names and encrypted passwords.
The vulnerability CVE-2023-35189 is the most serious of the issues since it allows an unauthenticated user to upload any file and then read it again from a web browser, which ultimately leads to command injection.
Threat actors might use the issues to access data from the server (configurations, logs, and databases), run arbitrary commands, and gain encrypted administrator passwords and decode them using a hardcoded key.According to the researchers, an adversary may take advantage of the vulnerabilities to log into the ScrutisWeb management panel as an admin, watch the actions of linked ATMs, activate management mode on the devices, upload files, and reboot or power off the machines.
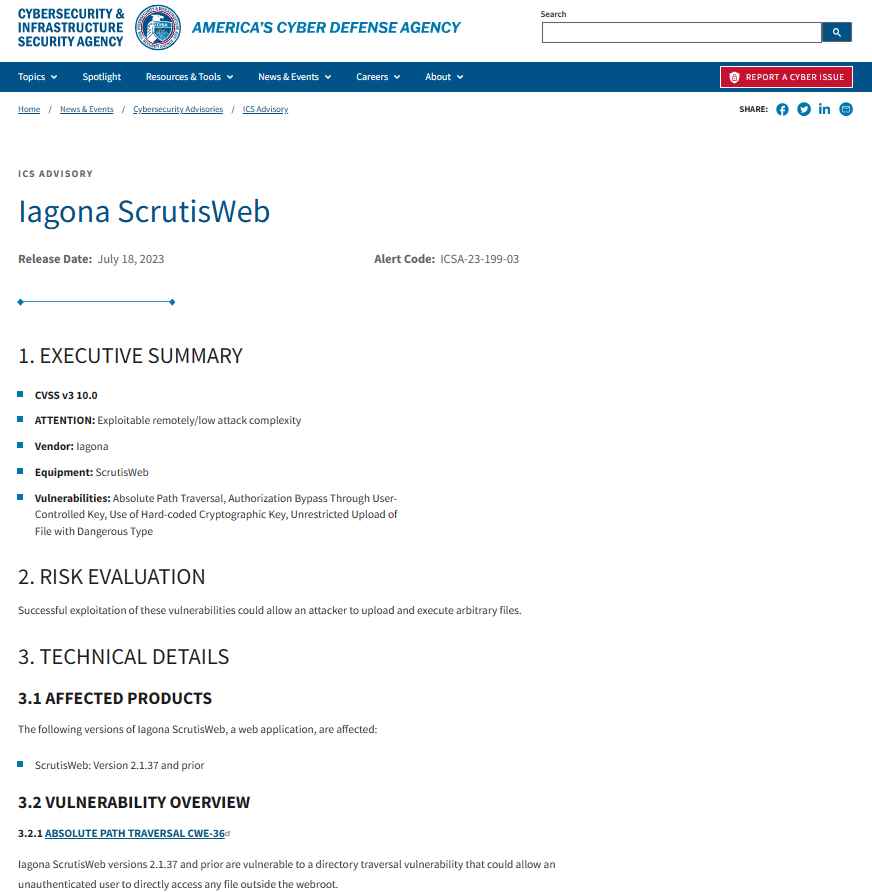
Hackers might potentially take advantage of the vulnerability that allowed remote command execution in order to cover their traces by deleting crucial data.Recently, the United States Cybersecurity and Infrastructure Security Agency (CISA) produced a warning with the purpose of informing enterprises about these vulnerabilities. CISA reports that the product in question is used all over the globe.

Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.











