In a striking revelation shaking the cybersecurity world, researchers have unearthed a sophisticated web shell, dubbed ‘HrServ,’ hidden within a seemingly innocuous DLL file, ‘hrserv.dll.’ This discovery, emerging from routine cybersecurity investigations, uncovers a new depth in the sophistication of cyber attacks, challenging existing defense mechanisms.
The Alarming Emergence of Web Shells in Cyber Warfare
Web shells, a relatively obscure term outside cybersecurity circles, represent a formidable threat in the digital age. They are malicious scripts or programs that hackers deploy on compromised web servers, enabling remote access and control. The discovery of HrServ marks a significant escalation in this digital arms race. Typically, web shells are rudimentary in nature, but HrServ breaks this mold with its advanced capabilities and stealthy operations, setting a new benchmark for cyber threats.
Stumbling Upon ‘HrServ’
The journey to unearthing HrServ began with the routine analysis of suspicious files. Researchers stumbled upon ‘hrserv.dll,’ initially not appearing to deviate from the norm. However, closer inspection revealed its true nature. The web shell exhibited unprecedented features, including custom encoding methods for client communications and the ability to execute commands directly in the system’s memory, a tactic that significantly complicates detection.
Decoding HrServ’s Sophisticated Mechanics
HrServ’s infection chain starts with the creation of a scheduled task named ‘MicrosoftsUpdate,’ which further executes a batch file. This file then facilitates the copying of ‘hrserv.dll’ into the crucial System32 directory, effectively embedding the malware deep within the system. From here, HrServ springs to life, initiating an HTTP server and managing client-server communication with intricate custom encoding, involving Base64 and FNV1A64 hashing algorithms.
The Ingenious GET Parameter Technique
One of the most striking aspects of HrServ is its utilization of a GET parameter technique in its HTTP requests, specifically the parameter ‘cp.’ The GET parameter technique used in the HrServ web shell attack involves using specific parameters in the URL of an HTTP GET request to trigger various functions within the malware. In this case, the parameter named “cp” plays a critical role. Different values of this “cp” parameter lead to different actions being executed by the web shell. For example:
- GET with cp=0: Calls
VirtualAlloc, copies a custom decoded NID cookie value, and creates a new thread. - POST with cp=1: Creates a file and writes the custom decoded POST data to it.
- GET with cp=2: Reads a file using the custom decoded NID cookie value and returns it in the response.
- GET with cp=4 and 7: Returns Outlook Web App HTML data.
- POST with cp=6: Indicates a code execution process, copying decoded POST data to memory and creating a new thread.
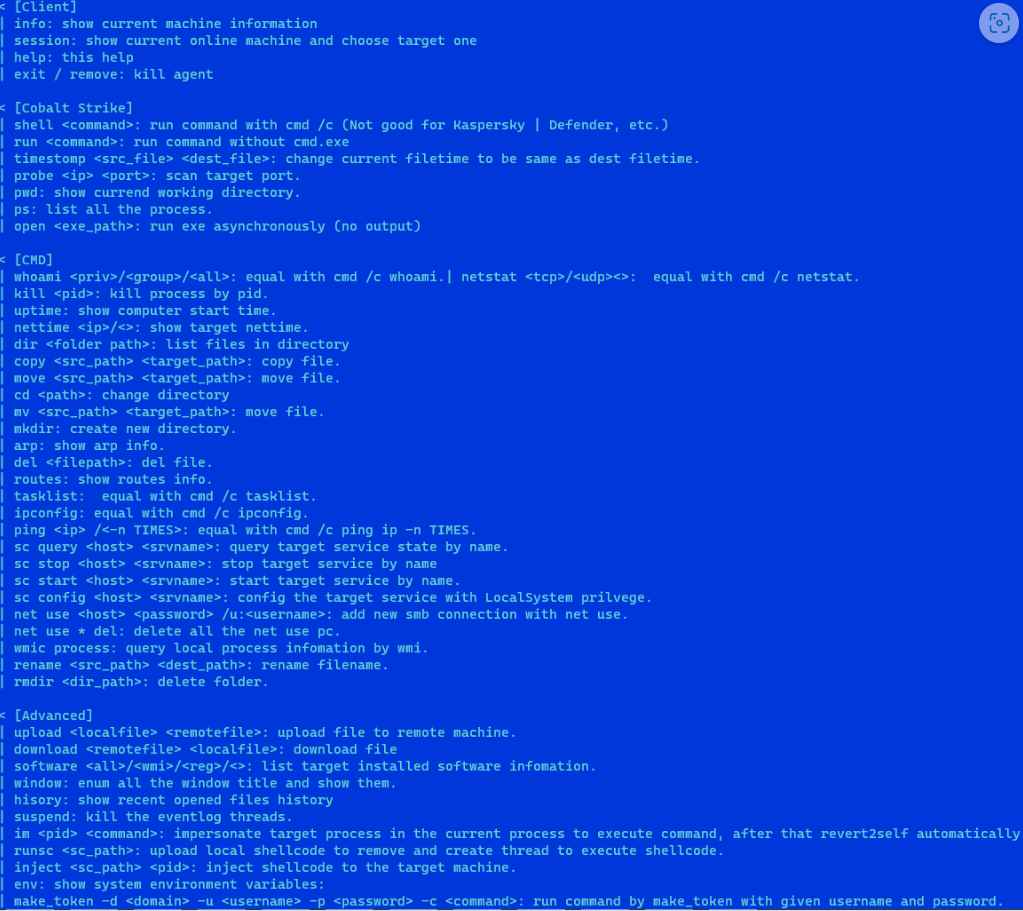
This technique allows the malware to perform various actions based on the HTTP request it receives, making it a versatile and dangerous tool for attackers. The use of common parameters like those found in Google services could also help mask the malicious traffic, blending it with legitimate web traffic and making detection more challenging.
Mimicking Google’s Web Traffic Patterns
In a cunning move to evade detection, HrServ’s communication pattern is modeled to mimic Google’s web services. This resemblance is not accidental but a deliberate attempt to blend malicious traffic with legitimate web services, making it a needle in a digital haystack for network monitoring systems.
The Afghan Government Entity: A Sole Victim with Global Implications
Remarkably, the only known victim of HrServ, as per the available data, was a government entity in Afghanistan. This targeted approach hints at the possibility of state-sponsored cyber espionage, although the attribution remains unclear. The implications of such a sophisticated attack extend far beyond a single entity, posing a stark reminder of the vulnerabilities inherent in digital infrastructures worldwide.
Unraveling the Mystery: Who is Behind HrServ?
The origins and affiliations of the HrServ creators remain shrouded in mystery. However, certain clues point towards a non-native English-speaking group, deduced from language patterns and technical intricacies observed in the malware. Moreover, the use of specific parameters akin to those in Google services suggests a high level of sophistication and understanding of global web traffic patterns.
Looking Ahead: A Cybersecurity Challenge for the Future
The discovery of HrServ represents a watershed moment in the ongoing battle between cybercriminals and defenders. Its sophisticated design, evasive techniques, and targeted application signify a new era in cyber threats, one where traditional defense mechanisms may no longer suffice. As cybersecurity experts continue to dissect and understand HrServ, the digital world braces for future challenges, emphasizing the ever-evolving nature of cyber threats and the perpetual need for innovative defense strategies.

Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.











