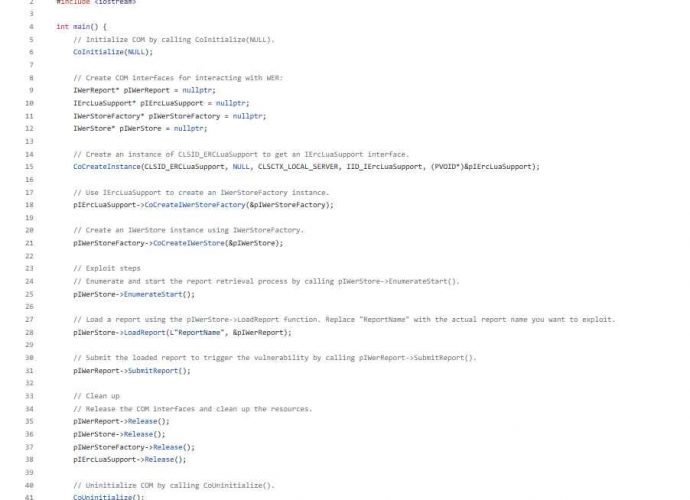
This code allow to hack into Juniper SRX firewalls and EX switches
Juniper Networks, a company that manufactures widely used networking equipment as well as security solutions, has issued a warning about vulnerabilities that are present in the operating systems of manyRead More →