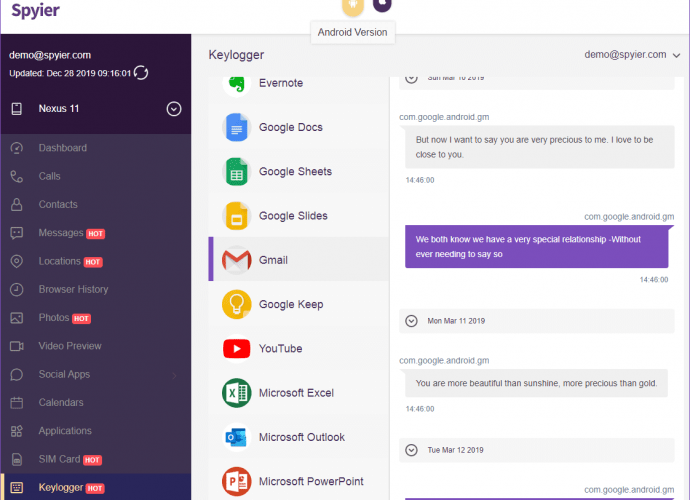
German police can see anyone’s WhatsApp messages at anytime, German media reports
Security measures in messaging platform WhatsApp are being questioned again. Computer forensics specialists mention that the German Federal Criminal Agency (BKA) has been able to access the messages on theRead More →