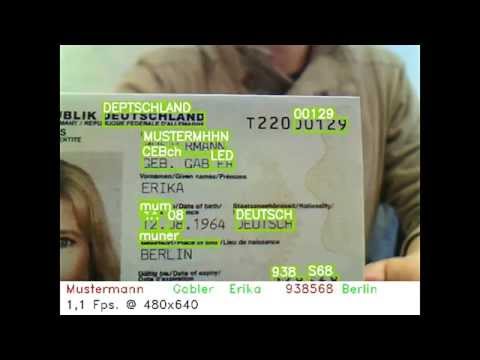
How to Extract Sensitive data (like username, access token or credit card) from picture
Introduction There are many instances where you want to extract something from the screenshots or pictures. Hackers uses some of these techniques to extract data from images. Now, we listRead More →