Inside LogoFAIL: The UEFI Firmware Flaw Compromising Millions of Devices
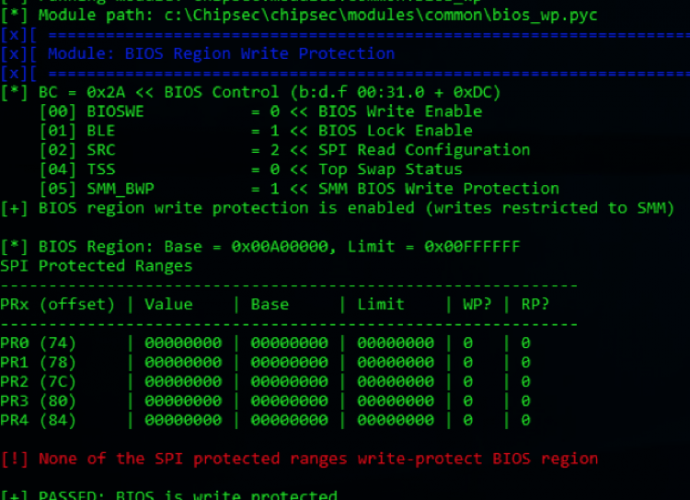
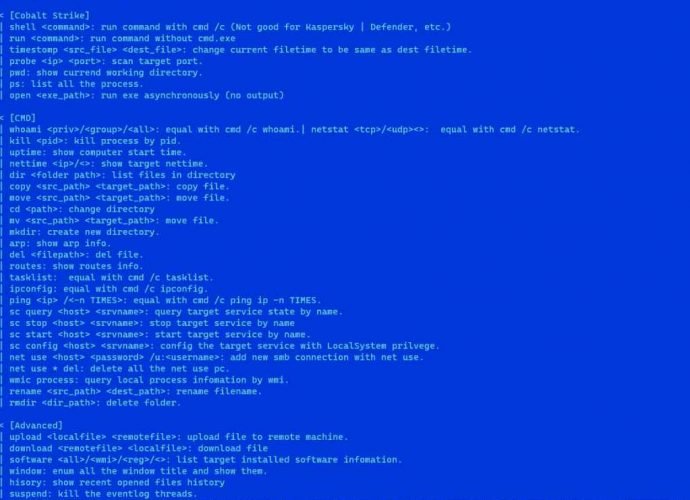
In the ever-evolving landscape of cybersecurity, a new threat has emerged, casting a long shadow over the integrity of computer systems worldwide. Dubbed ‘LogoFAIL,’ this set of vulnerabilities has beenRead More →