The Terrifying Reality of Citrix’s CVE-2023-4966 Vulnerability “Patching can’t help”
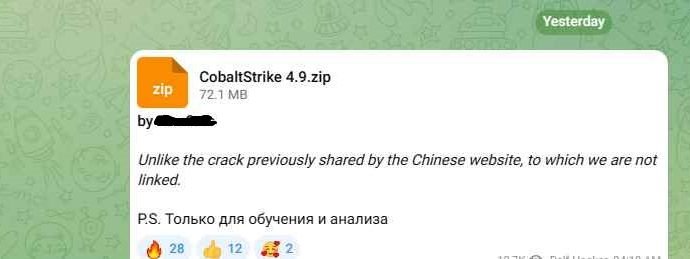
In a digital realm where security forms the bedrock of seamless operations, vulnerabilities act as ticking time bombs, waiting for exploitation. One such critical vulnerability, dubbed CVE-2023-4966, recently surfaced inRead More →