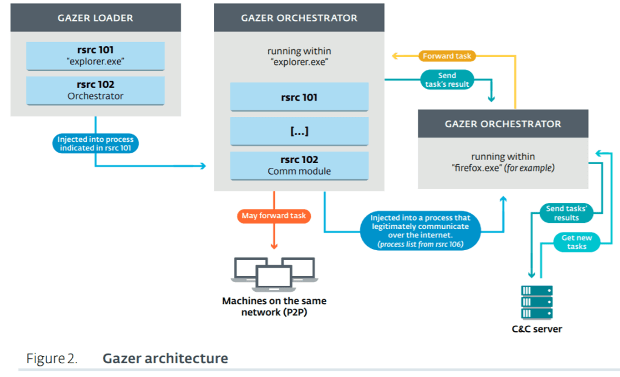
New ESET research uncovers Gazer, the stealthy backdoor that spies on embassies
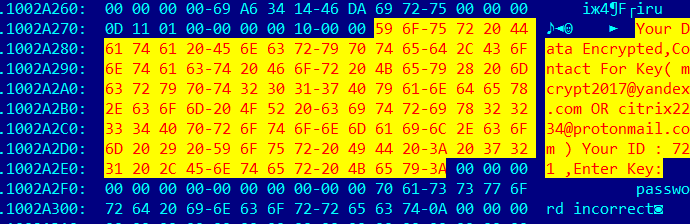
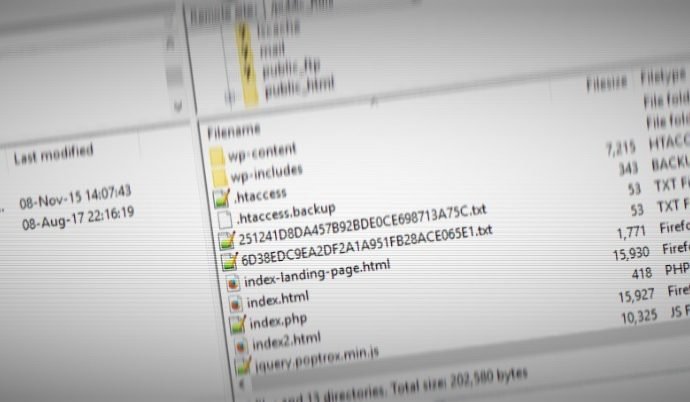
Security researchers at ESET have released new research today into the activities of the notorious Turla cyberespionage group, and specifically a previously undocumented backdoor that has been used to spy on consulatesRead More →