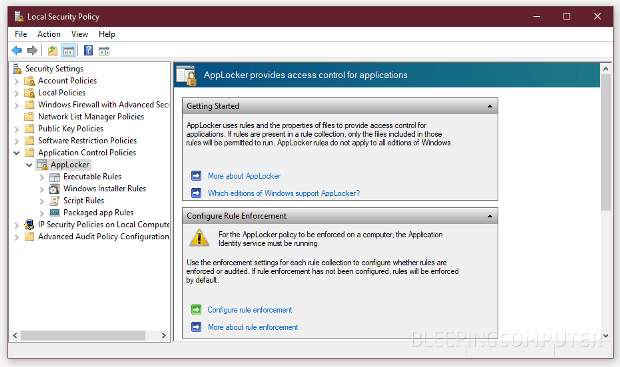
You Can Bypass Windows AppLocker Protection via Rogue Control Panel Items
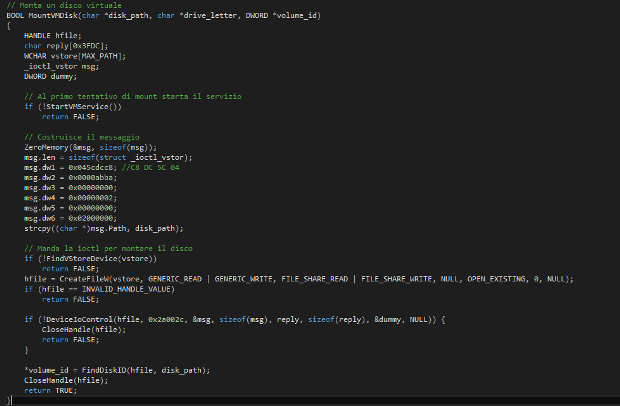
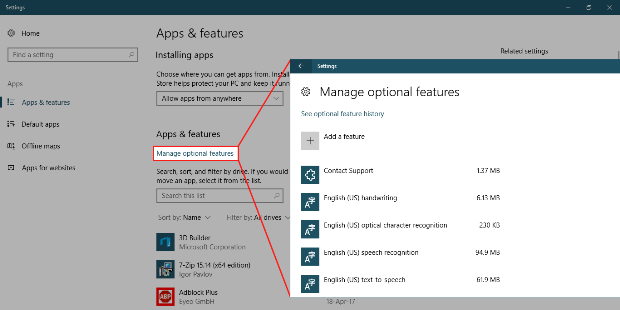
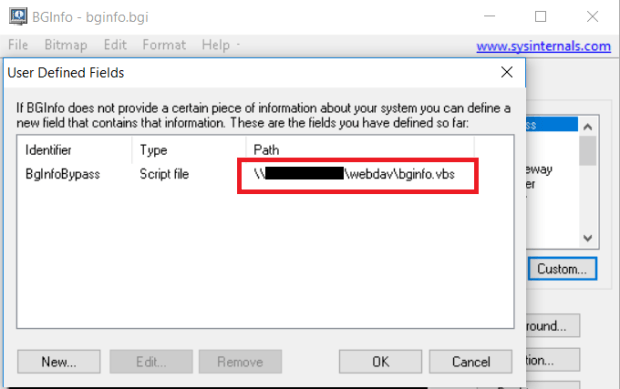
An attacker or a rogue employee can create and register custom control panel items and use these files to bypass the Windows AppLocker security feature. AppLocker is a security serviceRead More →