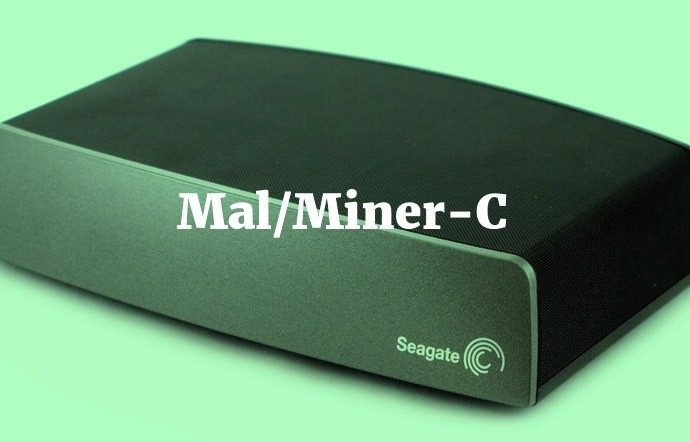
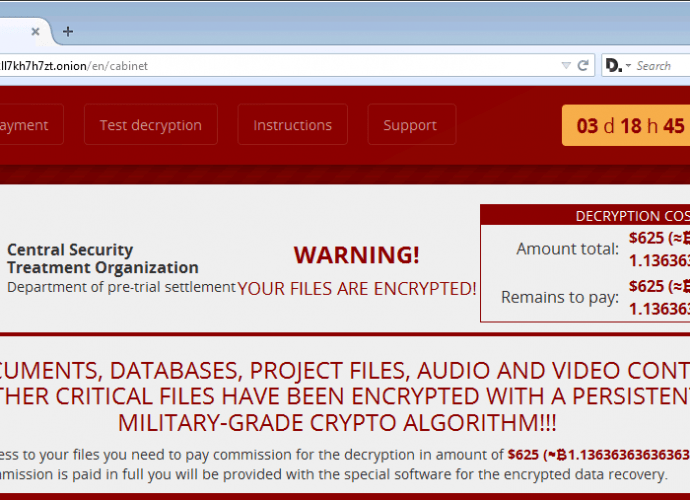
Cryptocurrency Mining Malware Discovered Targeting Seagate NAS Hard Drives
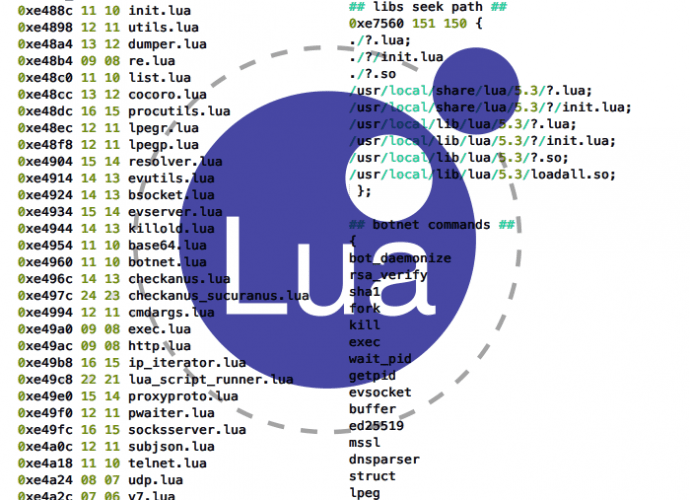
Malware authors have made around $86,400, so far. A malware variant named Mal/Miner-C (also known as PhotoMiner) is infecting Internet-exposed Seagate Central Network Attached Storage (NAS) devices and using them toRead More →