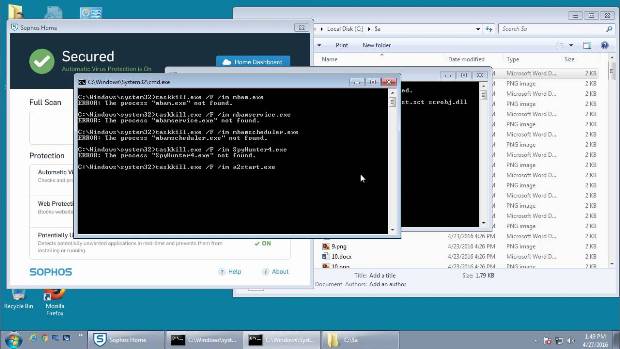
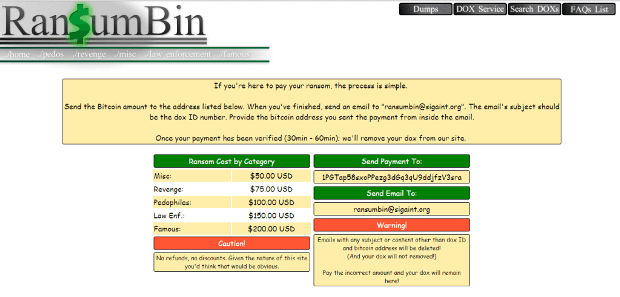
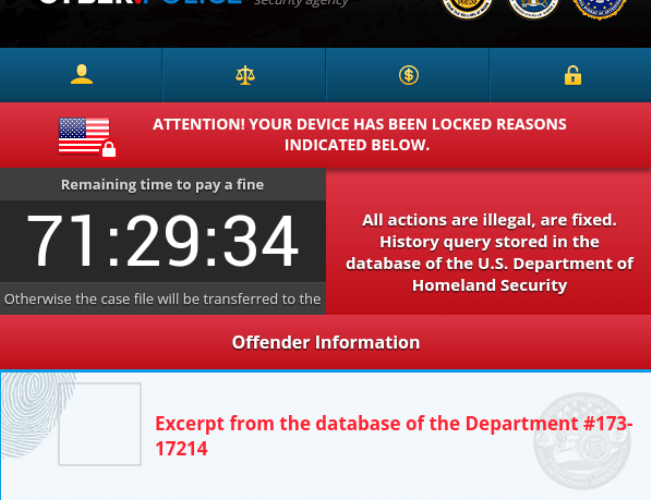
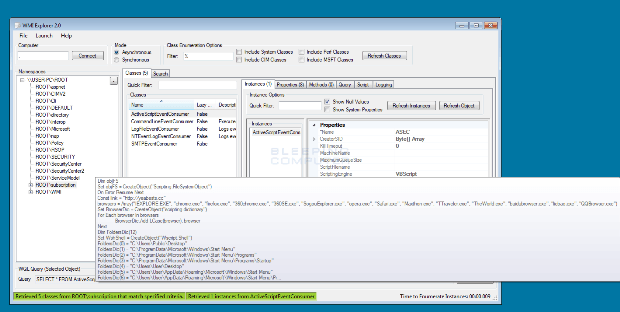
Regsvr32 can be used to install Ransomware through Jscript Installers
A security researcher named Casey Smith published an article last week where he detailed how the Windows Regsvr32.exe command could be used to bypass AppLocker restrictions. In this article he described a notRead More →