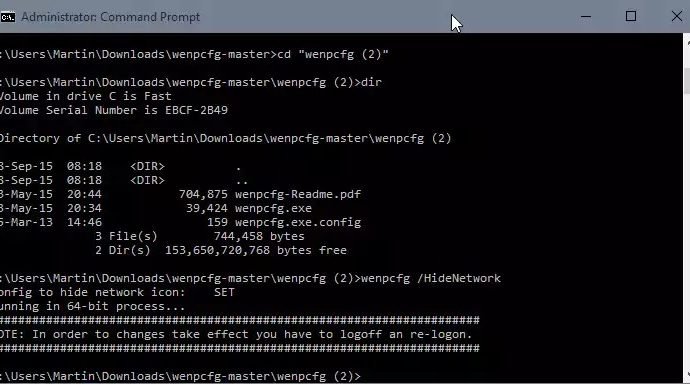
Remove Libraries, Network, Homegroup and other links from File Explorer
When you open File Explorer in Windows 10, the system’s default file browsing and management tool, you will notice immediately that it displays two panes in the main interface. TheRead More →