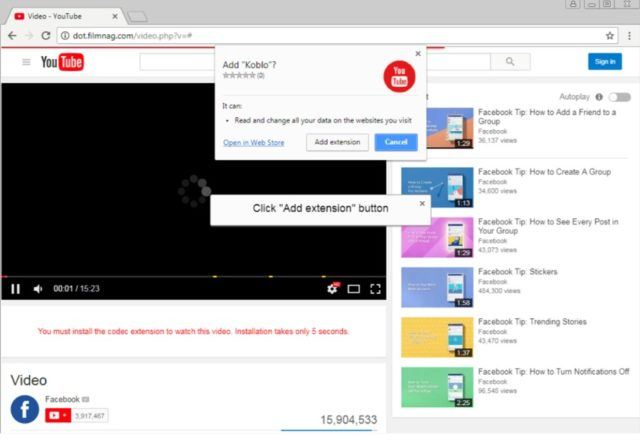
“FacexWorm” Fools Facebook Users And Steals Their Cryptocurrency And Login Credentials
Earlier this month, the security researchers at the firm TrendMicro spotted a new campaign related to FacexWorm that first surfaced last year. It targets Facebook users by sending them spam links inRead More →