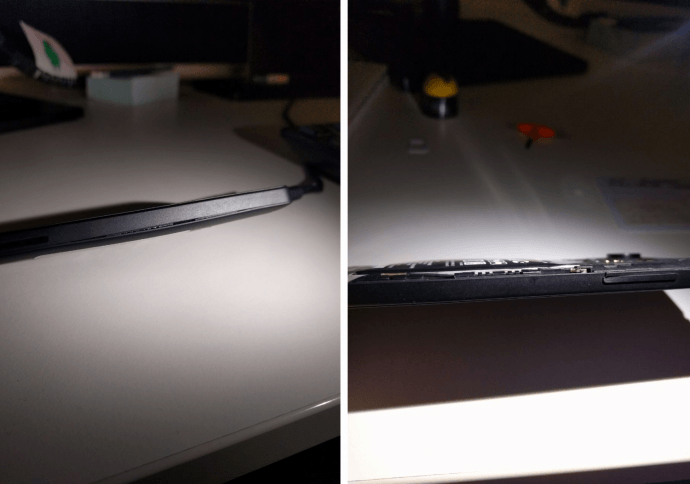
Android malware posing as porn can literally make your phone’s battery explode
A strain of Android malware found lurking on third-party application stores is so packed full of nefarious capabilities it can cause physical damage to smartphones. Security experts from Moscow-based anti-virusRead More →