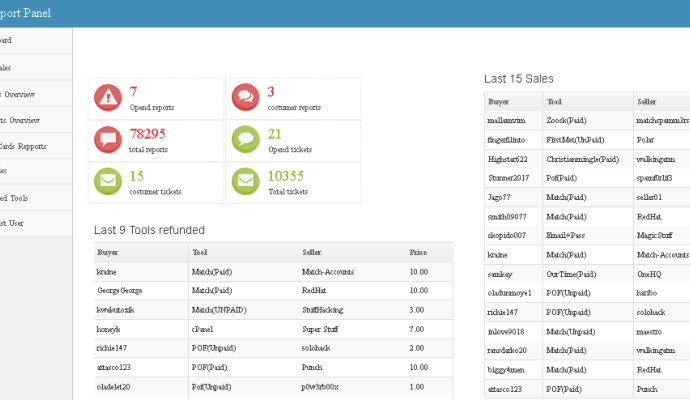
Basetools underground hacking forum breached, hacker demands $50K ransom
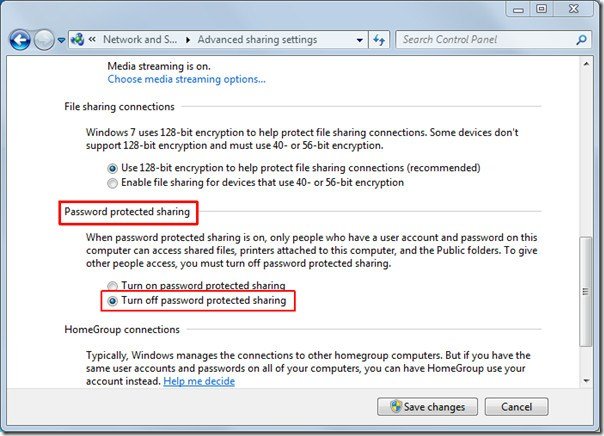
Basetools underground hacking forum was breached, hackers demand a $50K ransom to avoid sharing stolen data, including admin identity, with law enforcement. A hacker that goes online with the TwitterRead More →