ASD revealed hacker stole 30GB of sensitive data on Australia’s military capabilities
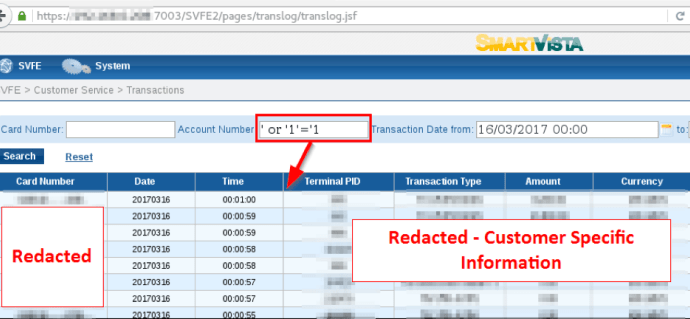
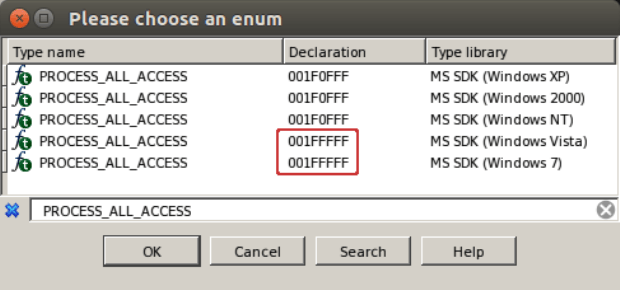
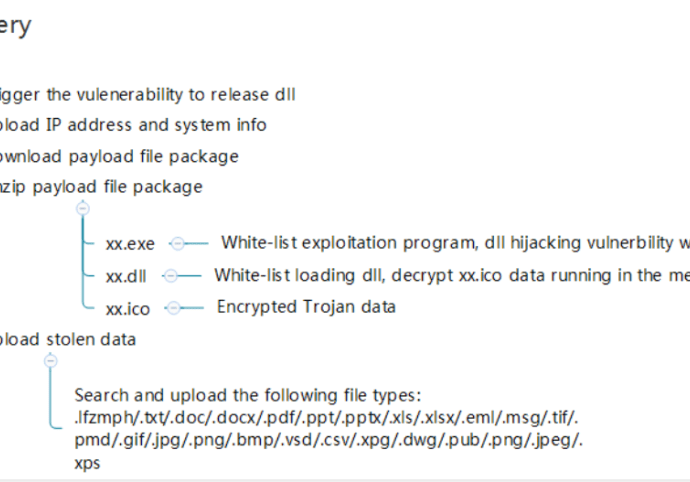
The Australia’s foreign intelligence Agency ASD has revealed military sensitive information has been stolen by hackers who breached a Department of Defence contractor. The Australia’s foreign intelligence agency, the Australian Signals DirectorateRead More →